Data Mapping Explained: A Practical Guide
Most organizations think they “know” their data.
They don’t.
They know systems. They know vendors. They know departments. But they do not know how personal data actually moves across their architecture.
And in today’s regulatory climate, that blind spot is not operational inconvenience — it is liability exposure.
Data Mapping gives you clear visibility of how personal data actually moves across your organization. Without it, your compliance policies remain theoretical.
Let’s fix that.
What Is Data Mapping?
Data Mapping is the structured documentation of how personal data flows through your organization — from collection to deletion. It identifies data sources, processing activities, storage locations, access controls, transfers, and retention timelines.
Regulators globally treat it as foundational evidence of accountability. Without it, you cannot demonstrate lawful processing or risk-based safeguards.
Data Mapping answers one unforgiving question: Where does personal data travel after you collect it?
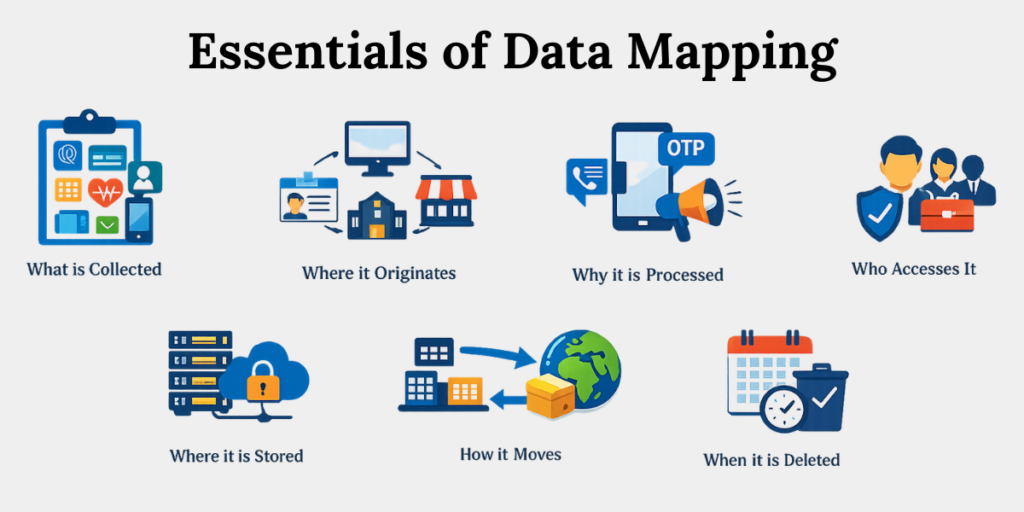
It documents:
1. What personal data is collected
Identify all categories of personal data collected across systems. This may include financial information (bank details, transaction history), identifiers (name, Aadhaar, PAN), biometric data, health records, employee records, educational details, and device identifiers. Mapping ensures no category is overlooked.
2. Where it originates
Document the source of collection. Data may originate from customers via websites, employees through HR systems, vendors via integrations, or third-party platforms. Knowing the source helps assess consent validity and lawful processing requirements.
3. Why it is processed
Define the exact purpose for each data field. For example, collecting a phone number for OTP verification is different from using it for marketing communication. Purpose clarity prevents misuse and supports compliance accountability.
4. Who accesses it
Identify internal teams and external vendors who access the data. For instance, HR may access payroll data, while customer support may access complaint records. Access must be role-based and documented to reduce unauthorized exposure.
5. Where it is stored
Map storage locations including on-premise servers, cloud platforms, SaaS tools, backup systems, and archived repositories. Storage visibility ensures security safeguards are implemented consistently across environments.
6. How it moves internally and externally
Track data flows between departments and to third parties. For example, customer data collected on a website may flow to CRM systems, marketing tools, and payment processors. Each transfer must be documented.
7. When it is deleted
Define retention timelines and deletion triggers. For example, resume data may be retained for six months, while transaction records may be retained for statutory periods. Mapping ensures data is not stored indefinitely.
Regulators increasingly expect demonstrable visibility.
Under frameworks like the EU GDPR (Article 30 ROPA obligations) and similar accountability-based models globally, organizations must prove structured oversight of processing activities.
[Source: https://gdpr.eu/article-30-records-of-processing-activities/]
Data Mapping builds that proof.
Why Is Data Mapping So Difficult for Organizations?
Data Mapping becomes difficult when organizations treat it as a one-time documentation task instead of an ongoing governance process. Disconnected systems, undocumented tools, third-party dependencies, and lack of executive oversight make it hard to maintain an accurate and updated view of data flows.
Let’s be honest.
Data hoarding is a habit. And bad habits rarely come with documentation.
Common failure points:
1. Relying on manual surveys instead of system-level discovery.
Many organizations send questionnaires to departments and compile answers into spreadsheets. This approach misses hidden integrations, APIs, and automated transfers that only technical system-level discovery can detect.
2. Ignoring shadow IT tools (marketing automation, SaaS subscriptions).
Marketing tools, SaaS subscriptions, and productivity platforms are often adopted without IT approval. These tools may collect and store personal data without being included in official documentation.
3. Failing to map cross-border transfers.
Cloud hosting, global vendors, and offshore teams may result in international data transfers. Without mapping these flows, organizations cannot assess legal safeguards or regulatory obligations.
4. Not updating maps after product launches.
New features, integrations, or mobile apps introduce new data flows. If maps are not updated regularly, documentation quickly becomes outdated and unreliable.
5. Confusing Data Inventory with Data Mapping.
A data inventory lists what data exists. Data Mapping explains how that data moves between systems, departments, and vendors. Treating both as the same leads to incomplete oversight.
Here’s the distinction:
- Data Inventory = What data exists.
- Data Mapping = How that data moves.
Inventory is static. Mapping is dynamic.
How Does Data Mapping Work in Practice?
Effective Data Mapping follows a structured lifecycle: identify data touchpoints, classify data types, map internal and external flows, document storage locations, assign ownership, and enforce retention triggers. It must be continuously updated to reflect system integrations, vendor onboarding, and new processing purposes.
Build it like an architect. Not like a clerk.
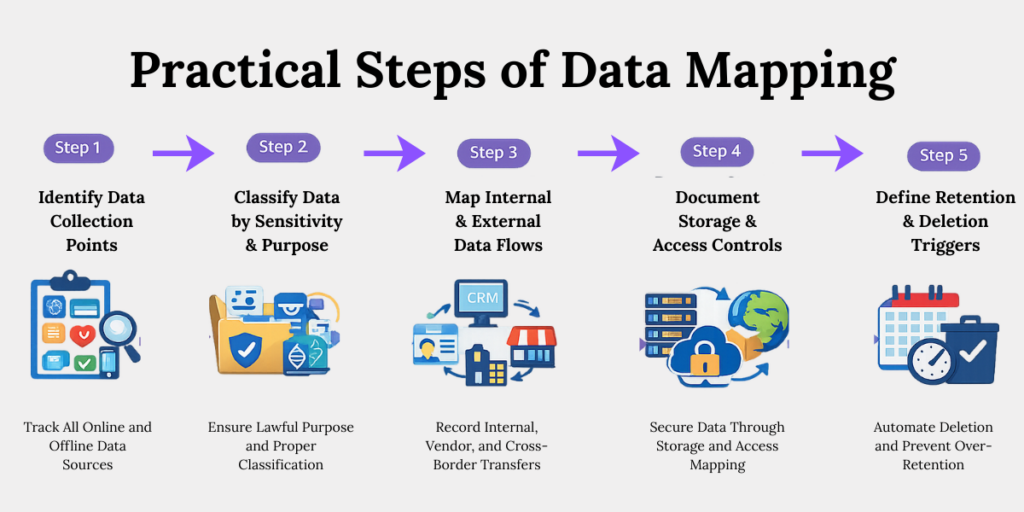
Step 1: Identify Data Collection Points
Map every entry gate.
1. Audit web forms, mobile apps, APIs, CRM inputs.
Review every digital touchpoint where users submit personal data. For example, contact forms, registration pages, payment gateways, and chatbot inputs may all collect different data categories.
2. Document HR systems and payroll platforms.
Employee data such as salary details, Aadhaar numbers, and bank accounts are processed through HR software. These systems must be included in mapping to ensure proper safeguards.
3. Trace customer onboarding workflows.
Map how customer data moves after initial signup. For example, onboarding data may flow from website forms to CRM systems, KYC verification tools, and email automation platforms.
4. Capture offline collection points (physical forms, call centers).
Physical forms, event registrations, call centers, and in-person onboarding also collect personal data. These sources must be documented alongside digital channels.
Miss one intake point, and your map fractures.
Step 2: Classify Data by Sensitivity & Purpose
Not all data is equal.
1. Categorize personal data vs. sensitive categories.
Separate general personal data (name, phone number) from sensitive categories such as financial or health data. Under the DPDP Act, 2023, organizations must implement reasonable security safeguards for each category of data. (Section 8 read with Rule 6 of DPDP Rules, 2025).
2. Tag children’s data where applicable.
If data relates to individuals under 18, additional safeguards apply. Rule 10 of the DPDP Rules, 2025 requires verifiable parental consent and restrictions on tracking or behavioural monitoring.
3. Define lawful purpose for each field.
Under Section 4 of the DPDP Act, processing must be for a lawful purpose with consent or legitimate use. Each data field must be linked to a clearly defined objective.
4. Link processing activity to business justification.
For example, collecting email addresses for invoice communication is valid, but using the same email for promotional campaigns requires proper consent. Mapping prevents unauthorized purpose expansion.
Regulators often penalize organizations for using data beyond its original purpose. Clear purpose mapping helps prevent that risk.
Step 3: Map Internal & External Data Flows
This is where most maps collapse.
1. Trace data movement between departments.
For example, sales teams may collect customer data that later moves to finance for invoicing and to support teams for service resolution. Each internal transfer must be documented.
2. Document integrations with SaaS tools.
CRM systems, email marketing platforms, analytics tools, and payment gateways process personal data. These integrations must be recorded to ensure oversight.
3. Identify sub-processors and cloud environments.
Cloud providers and third-party vendors may store or process personal data on your behalf. Their role must be clearly identified and documented.
4. Record cross-border transfers.
If data is stored or accessed outside India, document the destination country and applicable safeguards to meet regulatory expectations.
If you cannot trace the transfer, you cannot justify the safeguard.
Step 4: Document Storage & Access Controls
Map the vault.
1. Identify primary and backup storage locations.
Data may be stored in production servers and replicated in backup environments. Both locations must be documented to ensure consistent security controls.
2. Document encryption status.
Record whether data is encrypted at rest and in transit. For example, check if databases use AES-256 encryption and if data transfers use HTTPS protocols.
3. Record access roles (RBAC structures).
Define which roles can access specific data sets. For example, HR managers may access payroll data, but marketing teams should not.
4. Audit privileged account controls.
Monitor administrator accounts and super-user access. These accounts carry higher risk and require stricter logging and monitoring.
During investigations, regulators check whether employees had appropriate access. Clear access mapping reduces compliance risk.
Step 5: Define Retention & Deletion Triggers
Retention without discipline becomes liability.
1. Assign retention timelines per data category.
Define how long different types of data should be stored. For example, tax records may require longer retention than marketing leads.
2. Link deletion triggers to system automation.
Configure systems to automatically delete data once retention periods expire. Manual deletion increases the risk of oversight.
3. Prevent indefinite storage.
Avoid storing data “just in case.” Unnecessary retention increases breach exposure and regulatory scrutiny.
4. Schedule periodic map reviews (quarterly minimum).
Review and update data maps at least quarterly to reflect system changes, new vendors, or new processing activities.
Data minimization is not philosophy. It is operational risk control.
How Does Data Mapping Reduce Regulatory & Breach Risk?
Data Mapping reduces regulatory risk by demonstrating accountability, lawful processing, and risk-based safeguards. It accelerates breach containment, clarifies notification scope, and supports defensible documentation during audits. Organizations with structured mapping respond faster and reduce remediation costs significantly.
When a breach happens, panic spreads fast.
Without mapping:
- You guess affected systems.
- You over-notify regulators.
- You under-notify affected individuals.
- You scramble for vendor disclosures.
With mapping:
- You identify impacted datasets quickly.
- You isolate compromised nodes.
- You quantify affected individuals accurately.
- You respond within regulatory timelines.
Mapping accelerates containment.
Speed reduces fines.
What Does a Good Data Map Include?
A good Data Map includes data sources, data categories, processing purposes, legal bases, storage locations, access controls, vendor relationships, cross-border transfers, retention timelines, and deletion workflows. It must be version-controlled and periodically reviewed.
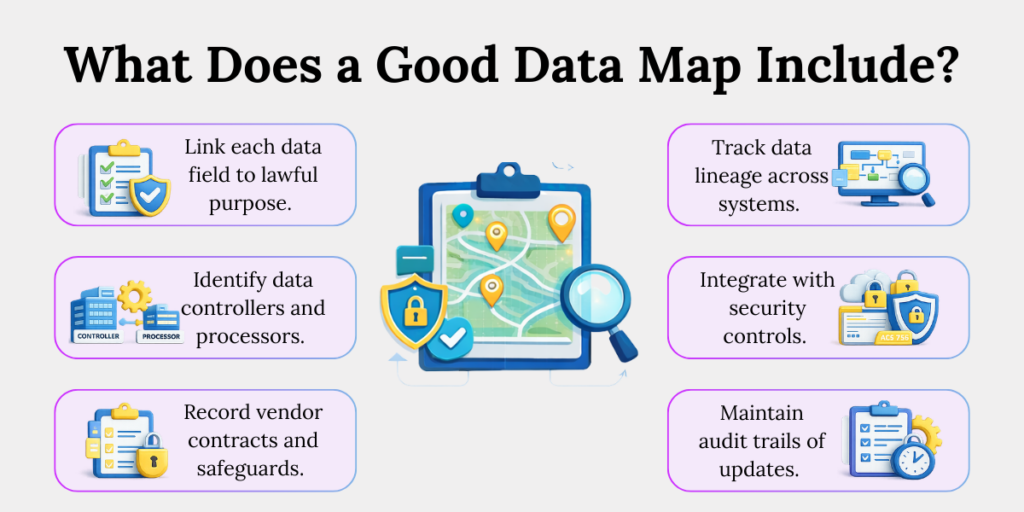
A mature Data Map must:
1. Link each data field to lawful purpose.
Every data element collected must have a documented purpose aligned with legal requirements.
2. Identify data controllers and processors.
Clarify whether your organization controls the data or processes it on behalf of another entity.
3. Record vendor contracts and safeguards.
Document data processing agreements, security clauses, and confidentiality obligations with vendors.
4. Track data lineage across systems.
Document how data moves from collection to storage, transformation, sharing, and deletion.
5. Integrate with security controls.
Ensure mapping aligns with access controls, encryption, logging, and monitoring mechanisms.
6. Maintain audit trails of updates.
Keep records of when the data map was updated and by whom to demonstrate ongoing governance.
Conclusion
Compliance is not built during an investigation. It is built before one.
Data Mapping transforms fragmented visibility into structured oversight. It turns policies into enforceable architecture. It shifts you from reactive defence to proactive governance.
Because in modern regulation, visibility is not optional — it is survival.
Key Takeaways
- Data Mapping shows how personal data moves across your organization and turns policy into practical control.
- It records what data you collect, where it comes from, why you use it, who can access it, where it is stored, and when it is deleted.
- Data Mapping fails when treated as a one-time document instead of an ongoing governance process.
- Start by identifying every data collection point, both digital and offline.
- Classify data by sensitivity and purpose to stay compliant and prevent misuse.
- Map internal, vendor, and cross-border data flows to maintain full visibility.
- Document storage, access controls, and retention timelines to reduce audit and breach risk.
- Keep your Data Map updated so it remains reliable evidence of accountability.



