Table of contents
February 24, 2026
Why DPDP Matters to E-commerce
E-commerce runs on personal data.
Under the Digital Personal Data Protection Act, 2023 (DPDP Act), that same data becomes a regulated asset with statutory liabilities attached. If you operate a marketplace, D2C brand, or platform in India, DPDP compliance for E-commerce is not optional compliance—it is structural risk management.
The average Indian e-commerce platform processes’ identity data, payment details, device identifiers, and behavioural analytics daily. India had over 900 million internet users in 2023 and crossed 250+ million online shoppers.
That’s not just traffic. That’s legal responsibility.
Let’s break the problem.
Why Is DPDP a Structural Issue for E-commerce?
DPDP matters to e-commerce because every transaction, login, targeted ad, and delivery update involves processing “digital personal data.” Under the Act, platforms act as “Data Fiduciaries” and face penalties up to ₹250 crore for security failures and ₹200 crore for breach notification lapses. The scale of data equals the scale of liability.
[Source: DPDP Act, 2023 – Schedule of Penalties]
E-commerce platforms collect:
- Names, addresses, phone numbers.
- Payment information and UPI identifiers.
- Order histories and preferences.
- Location data and device IDs.
- Children’s data in toy, gaming, and education categories.
For E-commerce data fiduciaries;
Under the DPDP Act:
- Rule 6 mandates “reasonable security safeguards.”
- Rule 7 mandates breach notification “without delay.”
- Rule 10 restricts processing of children’s data.
- Rule 13 imposes additional duties on Significant Data Fiduciaries.
You are not just selling products.
You’re running a system that handles legally protected data.
Ignore it, and problems will follow.
Is an E-commerce Company a Data Fiduciary Under DPDP?
Under DPDP, any entity determining the purpose and means of processing personal data is a “Data Fiduciary.” In e-commerce, this includes marketplaces, D2C brands, payment-linked sellers, and even app-based aggregators. The role carries legal accountability similar to a trustee handling someone else’s assets.
Think of a Data Fiduciary like the seller who holds the customer’s delivery address.
The buyer trusts you with their details. Misuse it, and the trust breaks immediately.
Generally, there are 3 common misunderstandings for digital marketplaces:
- Platforms assume logistics vendors carry liability.
- Sellers assume marketplaces carry liability.
- Marketing teams assume consent banners solve everything.
They don’t.
Liability follows control.
If you determine why data is collected, you are responsible under the law.
Security Requirements for E-Commerce Platforms
Rule 6 requires Data Fiduciaries to implement reasonable security safeguards to prevent personal data breaches. For e-commerce platforms handling millions of transactions monthly, this means encryption, access controls, monitoring systems, and vendor security validation are not best practices—they are legal obligations.
The penalty for failing to implement reasonable safeguards can reach ₹250 crore.
Security failures in e-commerce usually stem from:
1. Weak API integrations.
APIs connect your platform to payment gateways, logistics partners, and marketing tools. If these integrations lack authentication controls, encryption, or rate limits, attackers can exploit them as entry points into your system.
2. Insecure third-party plugins.
Plugins power reviews, chatbots, analytics, and promotions. Poorly coded or outdated plugins often contain vulnerabilities that expose customer data without the core system being directly breached.
3. Shared admin credentials.
When multiple employees use the same login credentials, accountability disappears. If something goes wrong, you cannot trace actions properly—and insider threats or accidental misuse become harder to control.
4. Unmonitored cloud storage buckets.
Cloud storage is often used for invoices, order logs, and backups. If storage buckets are misconfigured or left publicly accessible, sensitive customer data can be exposed without detection.
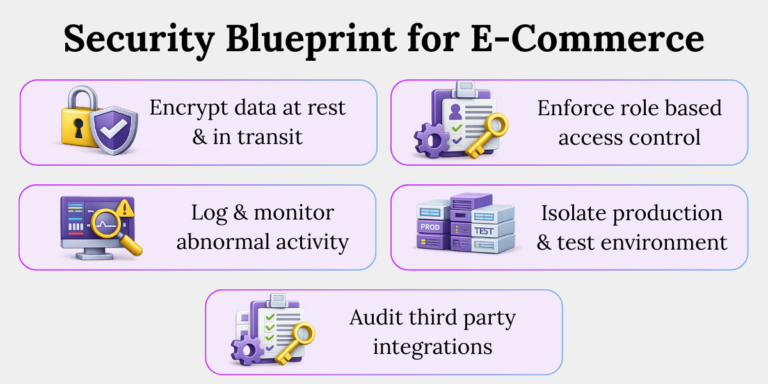
Implement this security blueprint:
1. Encrypt data at rest and in transit.
Encryption converts readable data into coded form so unauthorized users cannot understand it.
For example, if customer payment details are intercepted during transmission or accessed from a stolen server, encryption ensures the data remains unusable.
2. Enforce role-based access control (RBAC).
RBAC limits system access based on an employee’s job role.
For instance, a customer support agent should view order history but not download full payment databases. This reduces internal misuse and accidental exposure
3. Audit third-party integrations quarterly.
Regular audits review whether external vendors and plugins follow your security standards.
For example, if a logistics API updates its system and weakens authentication, a quarterly audit helps detect and fix the risk early.
4. Log and monitor abnormal activity.
Logging tracks who accessed what data and when, while monitoring flags unusual behaviour.
For example, if an admin account suddenly downloads thousands of user records at midnight, alerts allow immediate investigation.
5. Isolate production and test environments.
Production systems contain live customer data, while test environments should use dummy data. Separating them ensures developers do not accidentally expose real customer information while testing new features.
How Should E-Commerce Report Data Breaches?
Rule 7 requires notifying affected individuals and the Data Protection Board in case of a personal data breach without delay. For e-commerce platforms, this means incident response must be operationally ready before a breach occurs—not after it. Delays can trigger penalties up to ₹200 crore.
In recent global enforcement trends, regulatory action often penalizes delayed disclosure more harshly than the breach itself.
Ask yourself:
- Do employees report incidents within 24 hours?
- Do vendors have mandatory reporting clauses?
- Do you have pre-drafted customer communication templates?
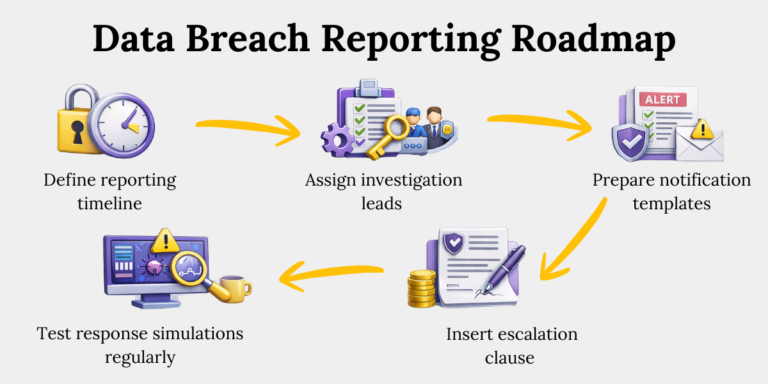
Build an incident roadmap:
1. Define internal reporting timelines (≤24 hours).
Set a clear rule that any suspected data incident must be reported internally within 24 hours.
For example, if a support agent notices unusual account activity, early reporting ensures the security team can investigate before the breach spreads.
2. Assign investigation leads.
Clearly identify who is responsible for leading breach investigations—IT, legal, compliance, or a designated response team. When roles are predefined, confusion is reduced and response time improves during a real incident.
3. Prepare regulator notification templates.
Draft standard formats for notifying the Data Protection Board and affected individuals. Having templates ready ensures you do not waste critical time drafting communication while the breach situation is escalating.
4. Insert vendor escalation clauses.
Include contractual terms requiring vendors to report breaches immediately.
For example, if a payment processor faces a security incident, you must be informed quickly to fulfil your own notification obligations.
5. Test response simulations regularly.
Conduct mock breach drills to evaluate your readiness. Simulations help identify gaps in coordination, reporting delays, or technical weaknesses before a real incident occurs.
Speed preserves credibility.
Silence amplifies damage.
Children’s Data in E-commerce
Under Rule 10 of the DPDP framework, processing children’s personal data requires verifiable parental consent and prohibits tracking or behavioural monitoring likely to cause harm. For e-commerce platforms selling toys, games, education tools, or family products, this is a high-risk category.
Penalty exposure: up to ₹200 crore.
Children’s data risks in e-commerce include:
1. Auto-filled parental accounts.
Many platforms allow parents to save payment details and addresses for faster checkout. When a child uses the same account to browse or place an order, their data gets processed without separate safeguards.
This creates compliance risk because children’s data requires stricter protection and verifiable parental consent under DPDP.
2. Behavioural advertising targeting minors.
E-commerce platforms often track browsing history to show personalized ads. If a child browses toys or games, the system may start profiling their behaviour automatically.
This is harmful because DPDP restricts tracking and targeted advertising that could exploit or influence minors.
3. Loyalty programs linked to children’s profiles.
Some brands create reward programs where children’s preferences, birthdays, or activity data are stored to offer discounts. In real life, these builds detailed behavioural profiles over time.
Such profiling increases regulatory risk because children’s data cannot be processed casually or for aggressive marketing purposes.
4. Gaming integrations.
E-commerce apps sometimes integrate mini-games or interactive features to increase engagement. When these games collect usernames, device IDs, or activity patterns from minors, data processing happens silently.
This becomes problematic because tracking children’s digital behaviour can violate DPDP safeguards and parental consent requirements.
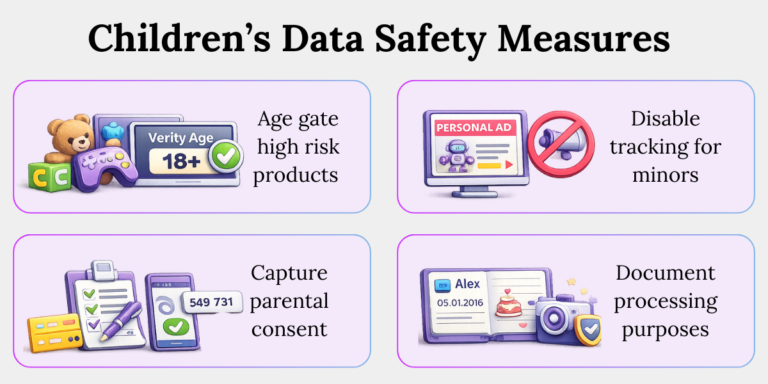
Implement safeguards:
1. Age-gate high-risk product categories.
Add an age verification step before allowing access to categories like toys, gaming products, or educational apps.
For example, if a child tries to create an account to buy a game, the system should first confirm they are above the required age or redirect to a parent. This reduces accidental collection of children’s data without safeguards.
2. Disable behavioural tracking for minors.
Turn off tracking tools like personalized ads, browsing history profiling, and targeted recommendations for identified minors.
For instance, if a child browses action figures, the platform should not start building a behavioural profile to push similar ads. This prevents profiling practices that DPDP restricts for children.
3. Capture verifiable parental consent.
Use clear methods to confirm that a parent or guardian has approved data processing. This could include OTP-based verification linked to the parent’s phone number or a verified payment method.
Simply asking a child to tick a checkbox is not enough under DPDP standards.
4. Document processing purposes clearly.
Maintain written records explaining why children’s data is collected and how it is used.
For example, if you collect a child’s name to deliver a personalized birthday gift, document that specific purpose and ensure it is not reused for marketing campaigns. Clear documentation protects you during audits or regulatory reviews.
Children’s data is not marketing fuel.
It is regulatory dynamite.
How Cross-Border Data Transfers Affect E-commerce Platforms
DPDP follows a “negative list” model for cross-border transfers, meaning data can be transferred outside India except to countries specifically restricted by the Central Government. However, accountability remains with the Data Fiduciary regardless of transfer location.
Most e-commerce platforms use:
- Global cloud providers.
- International payment gateways.
- Overseas analytics tools.
Here’s the reality:
You can transfer data. You cannot transfer liability.
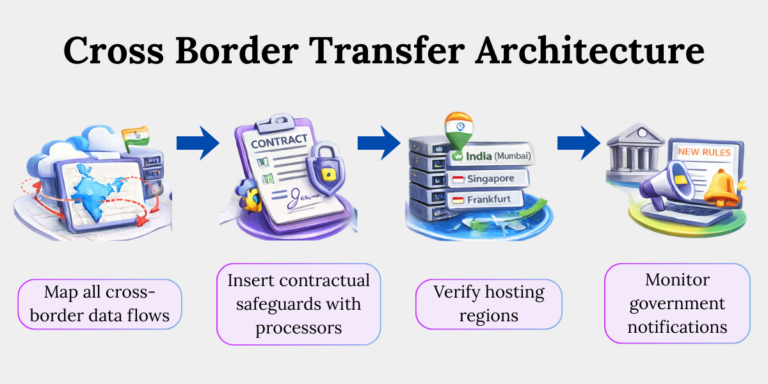
Strengthen your architecture:
1. Map all cross-border data flows.
Identify where customer data travels outside India—whether through cloud hosting, payment gateways, analytics tools, or CRM software.
For example, platforms using global cloud providers or international payment processors may be transferring order data abroad without realizing it.
Conduct a structured data mapping exercise internally or use a guided compliance assessment framework like the ones we implement at Privacy Global to document and control these flows before regulators ask.
2. Insert contractual safeguards with processors.
Update vendor agreements to include clear data protection clauses.
For example, contracts with payment processors or SaaS platforms should mandate encryption, breach reporting timelines, and audit rights. If your email marketing tool suffers a breach, the contract should require them to notify you immediately so you can comply with Rule 7 obligations.
3. Verify hosting regions.
Check where your data is physically stored. Many cloud providers allow you to select data centre regions such as Mumbai, Singapore, or Frankfurt.
Choose Indian regions where possible and document hosting locations internally. This reduces cross-border compliance complexity and prepares you if the government restricts transfers to certain jurisdictions.
4. Monitor government notifications.
DPDP allows cross-border transfers except to countries placed on a negative list by the Central Government. Assign someone in legal or compliance to monitor MeitY notifications and official government circulars regularly.
A simple monthly compliance review or regulatory alert subscription can prevent accidental violations if transfer rules change.
Global infrastructure does not dilute Indian compliance.
When Does an E-commerce Platform Become a “Significant Data Fiduciary”?
An entity may be designated a Significant Data Fiduciary (SDF) based on volume, sensitivity of data, risk to rights, and potential impact on national interests. Large e-commerce marketplaces handling millions of users may fall within this category.
SDF obligations include:
1. Appointing a Data Protection Officer.
A Data Protection Officer is a designated individual responsible for overseeing DPDP compliance and acting as the point of contact for regulators and customers.
In practical terms, this means having someone who reviews data practices, handles grievance redressal, and ensures breach notifications are filed correctly. For large e-commerce platforms, this role should be independent and report to senior management—not buried within IT operations.
2. Conducting Data Protection Impact Assessments.
A DPIA is a structured risk assessment carried out before launching high-risk data processing activities.
For example, if your platform introduces AI-driven personalized recommendations or facial recognition login features, a DPIA evaluates privacy risks in advance. This helps identify potential harm to users and implement safeguards before deployment.
3. Performing periodic audits.
Periodic audits involve reviewing systems, policies, and vendor practices to ensure ongoing compliance.
In real life, this could mean checking whether consent withdrawal actually works across all systems or verifying that access controls are properly enforced. Regular audits help detect gaps early and demonstrate accountability if regulators investigate.
Growth increases compliance weight.
Prepare before designation, not after notification.
How to Operationalize DPDP in E-commerce
Compliance is architecture.
Architecture requires design.
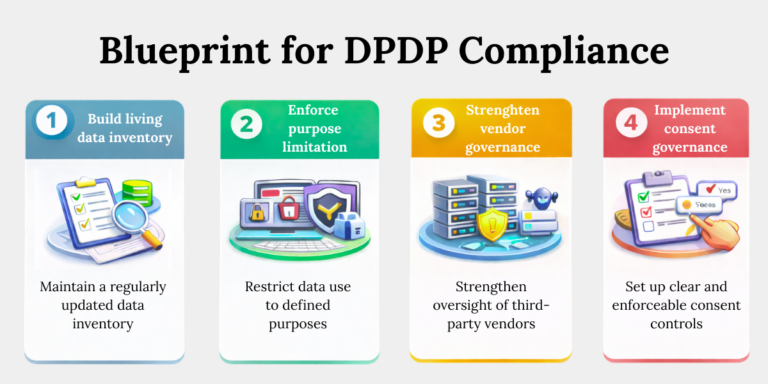
Follow this operational roadmap:
1. Build a Living Data Inventory
a. Identify every personal data touchpoint.
List every place where customer data is collected or stored—checkout pages, apps, CRM tools, payment gateways, and even chatbots. If a system touches customer information, it must be documented.
b. Classify by purpose, risk, and retention.
Define why each type of data is collected, how sensitive it is, and how long it should be kept. This prevents unnecessary storage and reduces exposure if a breach occurs.
c. Tag children’s and sensitive categories.
Label data related to minors or sensitive details like financial information. This ensures stricter safeguards are automatically applied where required.
d. Update quarterly.
Review the inventory every three months to capture new features, vendors, or integrations. E-commerce systems change fast—your documentation must keep up.
2. Enforce Purpose Limitation at System Level
a. Map data to defined business purposes.
Clearly link each data field to a specific business reason, such as order delivery, fraud prevention, or customer support. If you cannot explain why you collect it, you should not be storing it.
b. Block cross-purpose reuse technically.
Use system controls to prevent data collected for one purpose from being reused for another. For example, delivery address data should not automatically feed into marketing campaigns without separate consent.
c. Log internal access attempts.
Track who accesses customer data and when. If an employee tries to download bulk user records outside normal activity hours, logs help detect and investigate the risk quickly.
3. Strengthen Vendor Governance
a. Audit third-party processors.
List every place where customer data is collected or stored—checkout pages, apps, CRM tools, payment gateways, and even chatbots. If a system touches customer information, it must be documented.Regularly review vendors who handle customer data, such as payment gateways, logistics partners, and SaaS tools. Check whether they follow adequate security practices and store data securely, because their weakness becomes your liability.
b. Mandate breach reporting timelines.
Include clear clauses requiring vendors to inform you immediately if they experience a data breach. Early notification allows you to meet your own DPDP reporting obligations without delay.
c. Review data-sharing clauses annually.
Examine contracts every year to ensure data usage terms remain limited to agreed purposes. If a vendor expands services or changes systems, update the agreement to prevent silent over-collection or misuse.
4. Implement Consent Governance
a. Design granular consent capture.
Collect consent separately for different purposes, such as order updates, marketing emails, or personalized ads. This allows customers to choose what they agree to instead of accepting a single bundled permission.
b. Allow easy withdrawal.
Provide a simple way for users to withdraw consent, such as a clear unsubscribe link or account settings option. If stopping consent takes more effort than giving it, you increase compliance risk.
c. Propagate consent status across systems.
Ensure that when a customer withdraws consent, the update reflects across CRM, marketing tools, and analytics platforms. This prevents situations where marketing emails continue even after a user has opted out.
5. Create a Breach Response War-Room Plan
a. Simulate incidents.
Conduct mock data breach drills to test how your team responds under pressure. For example, simulate a leaked customer database and measure how quickly the issue is identified, escalated, and contained.
b. Train staff.
Educate employees on how to recognize and report potential data breaches. A support executive who spots unusual login activity should know exactly whom to inform and how fast to act.
c. Pre-draft regulatory submissions.
Prepare standard templates for notifying the Data Protection Board and affected customers. Having these drafts ready saves critical time when a real breach occurs and reduces the risk of incomplete disclosures.
This is not paperwork compliance.
This is operational discipline.
Conclusion
E-commerce thrives on speed and regulation demands structure.
The important thing to understand is, DPDP Act does not slow innovation—it forces discipline. Platforms that treat compliance as a defensive blueprint will build stronger customer trust, reduce litigation exposure, and withstand regulatory scrutiny.
Data is your revenue engine.
But under DPDP, it is also your compliance battlefield.
Build wisely.
Key Takeaways
- E-commerce platforms qualify as Data Fiduciaries under DPDP, meaning legal responsibility follows whoever decides why and how customer data is processed.
- Rule 6 makes security safeguards mandatory, requiring encryption, access controls, monitoring, and vendor oversight to prevent breaches.
- Rule 7 demands fast and structured breach reporting, so incident response plans must be ready before a crisis occurs.
- Children’s data is high-risk under Rule 10, requiring parental consent and strict limits on tracking or behavioural profiling.
- Cross-border transfers remain accountable under Indian law, even if data is stored or processed outside India
- Large platforms may be classified as Significant Data Fiduciaries, triggering obligations like appointing a DPO, conducting DPIAs, and performing audits.
- Operationalizing DPDP requires system-level discipline, including data inventory, purpose limitation, vendor governance, consent management, and breach readiness.
Related Blog
- https://www.privacyglobal.org/blog/dpdp-compliance-guide-for-education-sector
- https://www.privacyglobal.org/blog/dpdp-compliance-in-healthcare-sector
- https://www.privacyglobal.org/blog/why-dpdp-compliance-matters-for-bfsi-sector





