Table of contents
March 17, 2026 | 9 min read | Data Privacy
Top 5 Data Privacy Myth Debunked
Data privacy has become one of the most discussed topics in the digital economy. Yet, despite growing regulations and frequent headlines about data breaches and data leaks, many organisations still operate on dangerous assumptions.
These assumptions often take the form of a data privacy myth—widely believed ideas that sound logical but collapse under regulatory scrutiny. The result? Weak governance, compliance failures, and avoidable security incidents.
So where does the confusion start?
Let’s dismantle five of the most common myths.
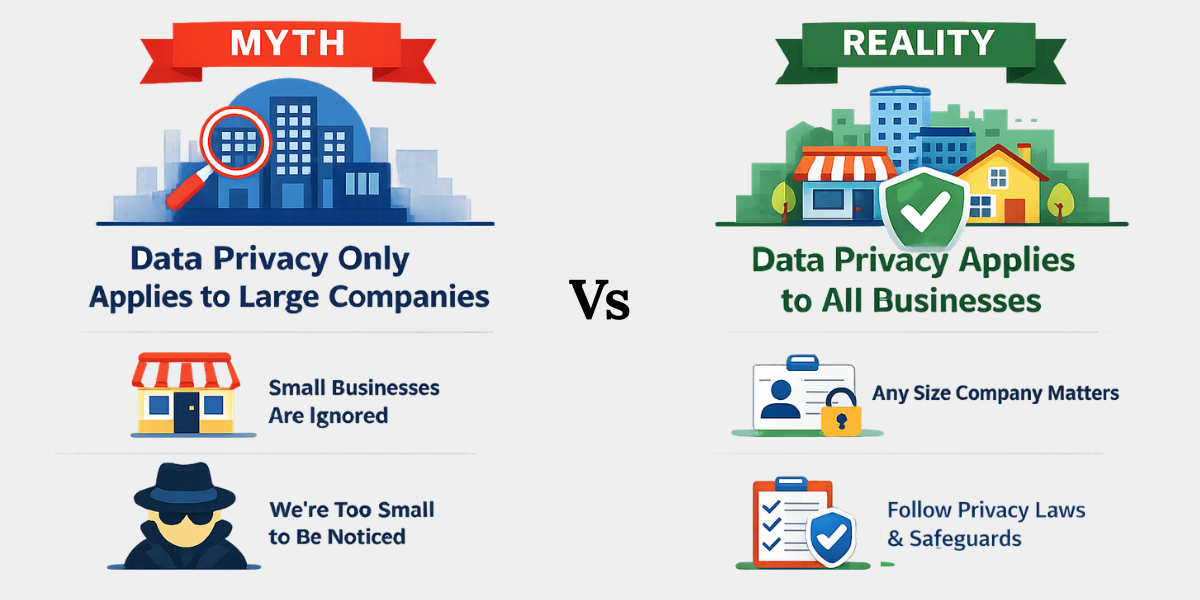
Myth 1: Data Privacy Only Applies to Large Companies
Many organisations assume data privacy for small businesses is not a priority. The belief is simple: regulators focus on big tech companies, not small startups or local businesses.
This myth exists because major privacy enforcement actions often involve global technology firms. Small companies mistakenly assume they are invisible to regulators.
Reality: Data privacy laws apply to any organisation that processes personal data, regardless of size.
Regulations such as India’s Digital Personal Data Protection Act, 2023 impose obligations on all data fiduciaries handling personal data. Even a small business collecting customer emails or phone numbers must implement lawful processing and security safeguards.
If your organisation collects:
- Customer contact information
- Employee data
- Payment details
- Website analytics data
then you are already handling personal data.
Privacy obligations are therefore not determined by company size, but by data processing activities.
Recommended Actions
-
Map the personal data you collect
Start by identifying what personal data your organisation collects and where it is stored. Many businesses discover hidden data flows in CRM systems, cloud tools, or marketing platforms. -
Implement basic privacy governance policies
Build internal policies for data retention, access control, and consent management. These policies form the foundation of responsible personal data protection. -
Assign accountability for privacy compliance
Even small organisations should designate someone responsible for privacy governance. Without accountability, privacy programs quickly collapse into confusion.
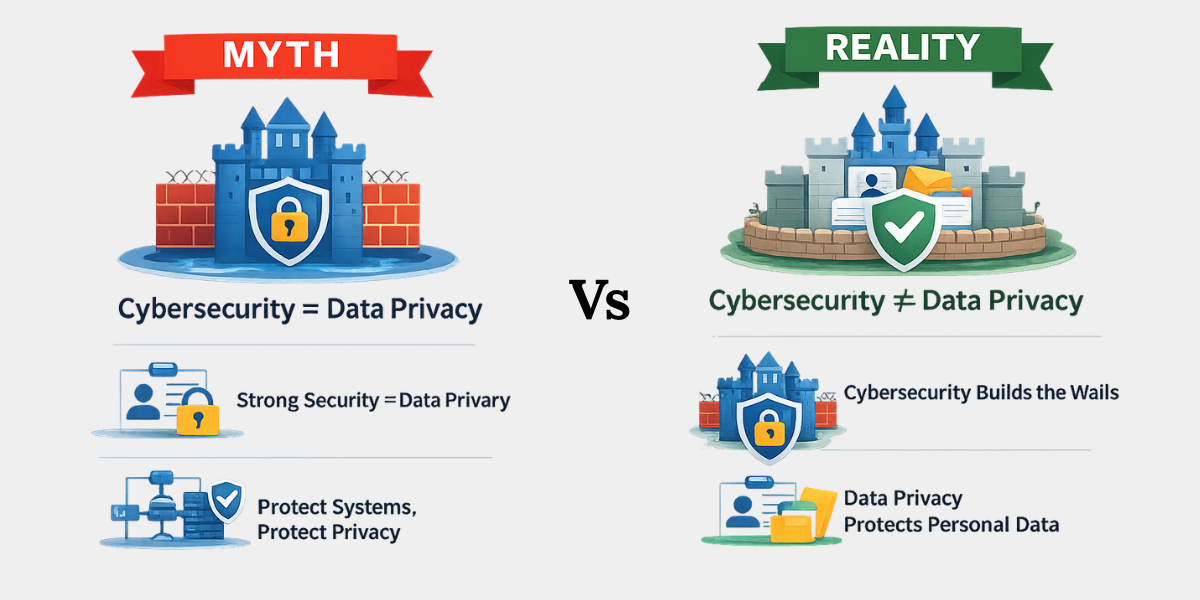
Myth 2: Cybersecurity and Data Privacy Are the Same Thing
A common misconception is that cybersecurity automatically guarantees data privacy.
Because both fields deal with protecting information, many organisations assume they are interchangeable.
Reality: Cybersecurity and data privacy serve different purposes.
Cybersecurity protects systems and networks from unauthorized access, while data privacy governs how personal data is collected, processed, and shared. An organisation may have strong cybersecurity defenses yet still violate privacy regulations through improper data usage or excessive data collection.
Think of it as a fortress.
- Cybersecurity builds the walls.
- Data privacy decides who is allowed inside.
A company could technically secure its servers yet still violate privacy regulations by:
- Collecting excessive personal data
- Sharing data without consent
- Retaining information longer than necessary
Privacy governance therefore focuses on lawful processing, not just technical protection.
Recommended Actions
-
Separate privacy governance from cybersecurity operations
Treat them as complementary disciplines. Cybersecurity teams protect infrastructure, while privacy teams manage data lifecycle compliance. -
Adopt data minimisation practices
Only collect the personal data necessary for a specific purpose. Excessive data collection increases privacy risks and regulatory exposure. -
Conduct privacy impact assessments
Evaluate how new systems or technologies process personal data. These assessments help organisations identify risks before deployment.
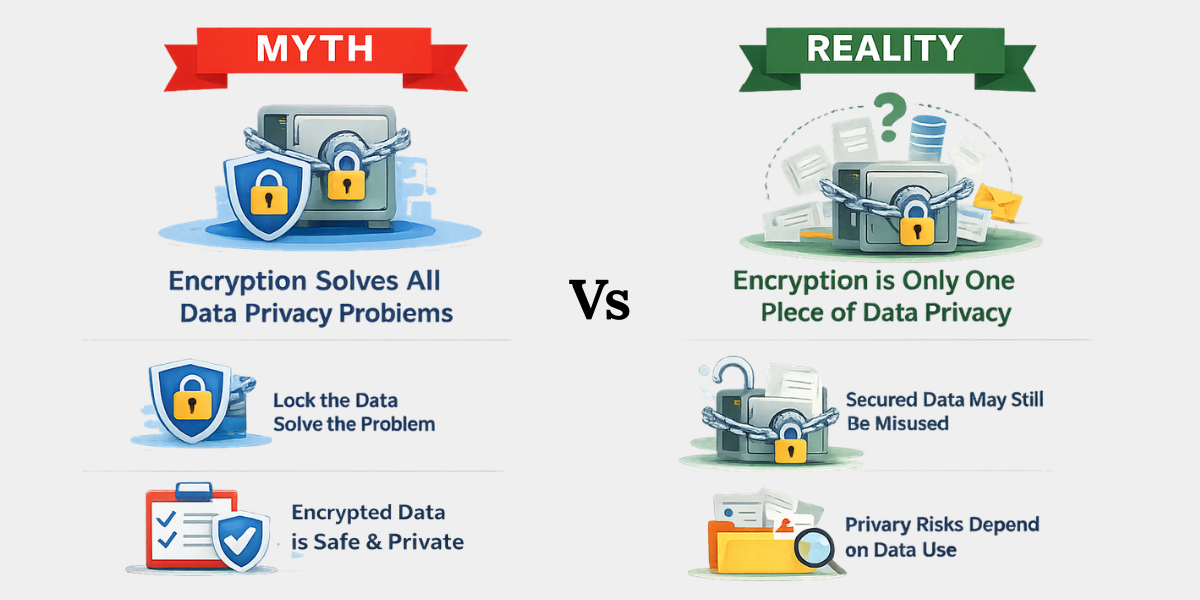
Myth 3: Encryption Solves All Data Privacy Problems
Many organisations believe encryption alone guarantees complete data protection.
Encryption is often marketed as the ultimate security solution. While it is powerful, it addresses only one dimension of privacy risk.
Reality: Encryption protects data from unauthorized access but does not ensure lawful or ethical data processing.
Privacy risks still arise when organisations collect excessive personal data, misuse it for secondary purposes, or share it improperly. Encryption secures the container—but privacy determines whether the data should exist there in the first place.
Consider a simple analogy.
Encryption is like locking a safe.
But privacy governance decides whether sensitive information should be stored in the safe at all.
Many major data breaches occur not because encryption failed but because organisations collected unnecessary personal data or stored it improperly.
Recommended Actions
-
Combine encryption with governance controls
Encryption must be supported by policies covering access control, retention periods, and data sharing. -
Apply purpose limitation principles
Collect personal data only for specific and legitimate purposes. Avoid repurposing information without consent. -
Audit third-party data processors
Many privacy incidents occur through vendors handling sensitive data. Ensure partners follow strong data protection standards.
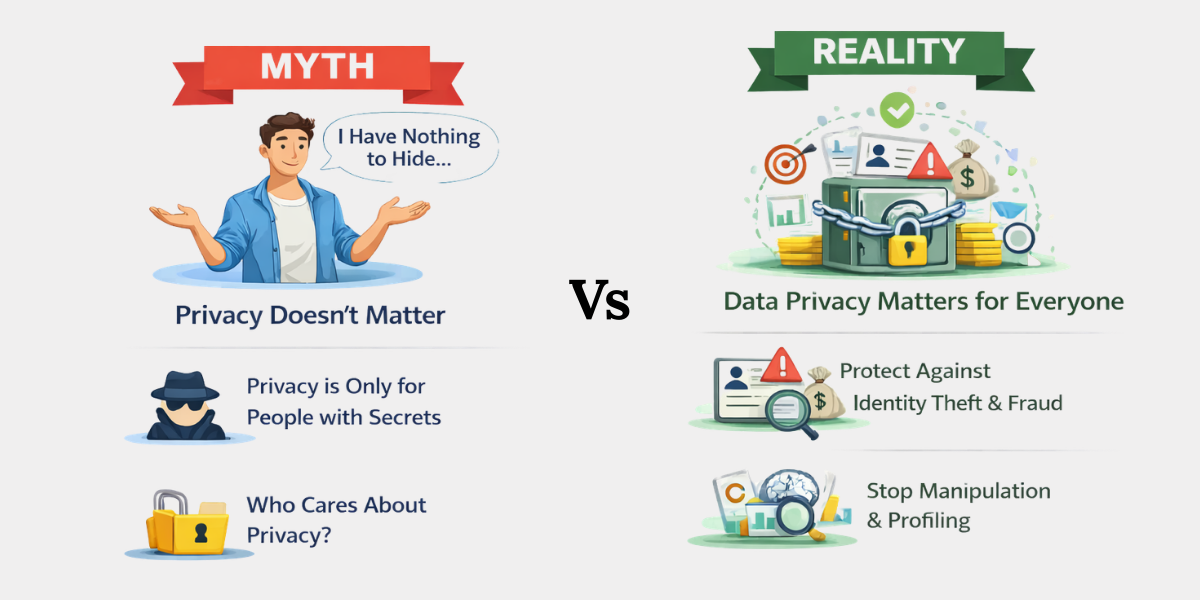
Myth 4: “I Have Nothing to Hide, So Privacy Doesn’t Matter”
Some individuals believe privacy is only important for people hiding something.
This mindset often appears when discussing surveillance, tracking technologies, or digital profiling.
Reality: Data privacy is not about hiding secrets—it is about maintaining control over personal information.
Even seemingly harmless personal data can be used for identity theft, financial fraud, targeted manipulation, or behavioural profiling. Without privacy protections, individuals lose the ability to control how their data influences decisions about them.
Consider how digital services operate today.
Platforms routinely analyse AI-driven behavioural data, including:
- Browsing patterns
- Location data
- Purchase behaviour
- Device usage
This information fuels targeted advertising, recommendation systems, and automated decision-making.
Without privacy safeguards, these systems can enable manipulation, discrimination, or intrusive surveillance.
Recommended Actions
-
Limit unnecessary data sharing
Share personal data only when it is necessary to access a service. Providing less information reduces the risk of misuse or exposure in a data breach. -
Review privacy settings regularly
Many platforms offer privacy controls but keep them at default settings. Adjusting these settings can help limit tracking and data sharing. -
Understand how digital platforms use data
Review privacy policies to understand how your personal data is collected, used, and shared. This helps you make informed decisions about the platforms you use.

Myth 5: Data Breaches Only Happen Because of Hackers
Many people believe cybercriminal hackers are responsible for most data breaches.
Media coverage often highlights dramatic cyberattacks, reinforcing the belief that external threats are the primary cause.
Reality: A large percentage of data breaches are caused by internal failures such as human error, misconfigured systems, or insider misuse.
Accidental data leaks—like exposed cloud databases or incorrectly shared files—frequently expose sensitive personal data without any sophisticated cyberattack.
Some of the most common breach causes include:
-
Misconfigured cloud storage
This occurs when cloud databases or storage folders are mistakenly left publicly accessible due to incorrect security settings. As a result, sensitive data becomes visible to anyone with internet access.
-
Employees emailing sensitive data incorrectly
Human error can lead to accidental data leaks. Employees may send confidential files to the wrong recipient, attach sensitive documents in reply-all emails, or forward internal reports outside the organisation.
-
Weak access control policies
Problems arise when employees have access to data they do not actually need. If an account is compromised, attackers can access large volumes of sensitive information. In many cases, organisations discover that former employees still retain access to internal systems.
-
Unsecured APIs
Security gaps in APIs can allow attackers to retrieve sensitive data directly from systems. In some incidents, attackers have accessed customer information by manipulating API requests due to missing authentication or weak security controls.
These incidents are often described as data leaks rather than attacks, yet their impact can be equally severe.
Recommended Actions
-
Train employees on data protection practices
Human error remains one of the leading causes of privacy incidents. Employees may unintentionally expose sensitive information through incorrect data handling, misdirected emails, or unsafe file sharing. -
Implement strict access control policies
Access to sensitive personal data should be limited to only those who genuinely need it for their role. Clearly defined access permissions reduce the risk of internal misuse and prevent large-scale exposure if an account is compromised. -
Conduct regular security and privacy audits
Routine audits help organisations identify weaknesses in their data protection practices. These reviews can uncover misconfigured systems, excessive data access, or outdated security controls before they lead to serious data breaches or leaks.
Conclusion
Data privacy myths persist because they simplify a complex subject. Unfortunately, these simplified beliefs often lead organisations down risky paths.
A modern privacy program requires more than technical security. It requires governance, accountability, and a clear understanding of how personal data flows through the organisation.
Think of privacy as a blueprint for a digital fortress.
Cybersecurity builds the walls.
Policies define the rules.
Governance ensures the fortress protects what matters most—personal data.
Key Takeaways
- Data privacy laws apply to organisations of all sizes, and any business that collects or processes personal data must follow applicable regulations and safeguards.
- Cybersecurity and data privacy are not the same, as cybersecurity protects systems while data privacy governs how personal data is collected, used, and shared.
- Encryption alone cannot ensure data privacy, because proper governance, purpose limitation, and responsible data handling are also essential.
- Data privacy is about maintaining control over personal information, not about hiding secrets, especially in an era of AI-driven data analysis and profiling.
- Many data breaches are caused by internal issues such as human error, weak access controls, and misconfigured systems, rather than sophisticated cyberattacks.
- Effective data protection requires a combination of governance, employee awareness, and strong security practices to reduce privacy risks and prevent data leaks.
Related Blog





