Table of contents
March 20, 2026 | 10 min read | DPDP
Consent Management Framework under the DPDP Act
Most organizations believe they “have consent.” In reality, they only have a checkbox and a timestamp. That’s not a consent management framework.
Under the Digital Personal Data Protection Act 2023 (DPDP Act), consent must be free, specific, informed, unconditional, and unambiguous.
If your systems cannot prove these elements through logs, controls, and withdrawal mechanisms, the consent may not survive regulatory scrutiny.
So, the real challenge is not collecting consent.
The real challenge is building a defensible consent architecture.
This article provides a practical roadmap for building a Consent Management Framework under the DPDP Act.
What is a Consent Management Framework?
A Consent Management Framework is the operational structure that allows an organization to collect, store, manage, enforce, and audit consent in accordance with the DPDP Act and DPDP Rule 3. It integrates legal requirements with technical systems such as consent management platforms, audit logs, purpose mapping, and withdrawal mechanisms to ensure consent remains valid throughout its lifecycle.
Consent is not a one-time action. It must be managed throughout its lifecycle.
Organizations must manage:
1. Consent Collection
Capture clear, affirmative user permission for specific data processing purposes.
2. Consent Validation
Ensure the consent meets legal requirements such as being free, specific, informed, and unambiguous.
3. Consent Storage
Securely record consent details, including timestamp, purpose, and consent language.
4. Consent Enforcement
Ensure all data processing strictly follows the permissions granted by the user.
5. Consent Withdrawal
Provide simple mechanisms for users to revoke their consent at any time.
6. Consent Auditing
Regularly review consent records to verify compliance with approved purposes.
Without this lifecycle approach, consent quickly becomes legally fragile.
Think of consent like a security clearance badge inside your data fortress. It grants access only for specific doors. If the badge allows access everywhere, the system has failed.
How Should a Consent Management System Work?
A Consent Management System (CMS), under the DPDP Act, must record when consent was obtained, what purpose it covers, how it was presented to the user, and whether it was withdrawn. The system must also maintain an audit trail that demonstrates compliance with DPDP Rule 3 requirements.
A compliant Consent Management System therefore needs four foundational layers.
1. Consent Capture Layer
This layer handles how consent is collected from the user.
Consent under the DPDP Act must be:
- Clear and affirmative
- Specific to the processing purpose
- Free from coercion
This means pre-ticked boxes or bundled consent statements are unlikely to qualify as valid consent.
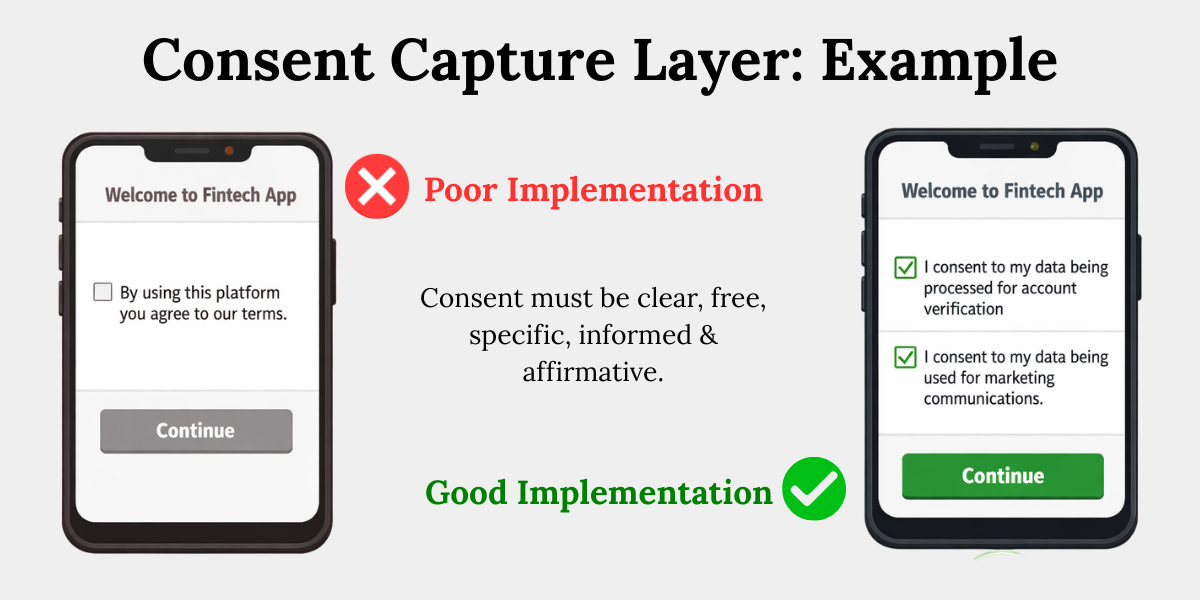
Example in practice
A fintech platform collects consent during onboarding.
Poor implementation:
“By using this platform you agree to our terms.”
Better implementation:
“I consent to my data being processed for account verification.”
“I consent to my data being used for marketing communications.”
This design introduces granular consent mechanisms, which regulators increasingly expect.
2. Consent Storage and Logging
Consent must be stored in a way that allows organizations to prove compliance during audits or investigations.
A strong consent logging and audit trail system should record:
Timestamp of consent
Record the exact date and time when the data principal provided consent. This helps demonstrate when the consent was obtained and whether it was valid at the time of data processing.
Identity of the data principal
Store a reliable identifier of the user who provided consent, such as a user ID, account number, or email. This ensures the consent can be clearly linked to the correct individual.
Consent text shown to the user
Log the exact consent notice or wording that was displayed when the user gave consent. This allows organizations to prove what information the user agreed to at that moment.
Purpose associated with consent
Record the specific purpose for which the consent was obtained, such as account creation, marketing communication, or analytics. This ensures data is processed only for the purposes the user agreed to.
Method of consent capture (web form, app, API)
Document how the consent was collected, whether through a website form, mobile application, or API integration. This helps demonstrate the mechanism used to obtain the user's affirmative action.
Without this information, the organization cannot demonstrate valid consent under the DPDP Act.
3. Purpose Mapping and Enforcement
Consent is only valid for the specific purpose for which it was obtained. This principle reflects purpose limitation under DPDP.
A consent management framework must therefore map each consent record to a specific processing activity.
Example
A healthcare app collects consent to process patient data for appointment scheduling.
If that same data is later used for targeted advertising, the original consent may become invalid.
This is where many organizations stumble.
Data silently travels across departments—analytics teams, marketing platforms, data lakes—without the original consent conditions following it.
A mature consent management system ensures that data processing engines respect consent boundaries automatically.
What Makes Consent Valid under the DPDP Act?
Under DPDP Rule 3, consent must be free, specific, informed, unconditional, and unambiguous. Organizations must translate these legal requirements into system design, consent interfaces, and governance controls.
Let’s translate these legal terms into practical implementation requirements.
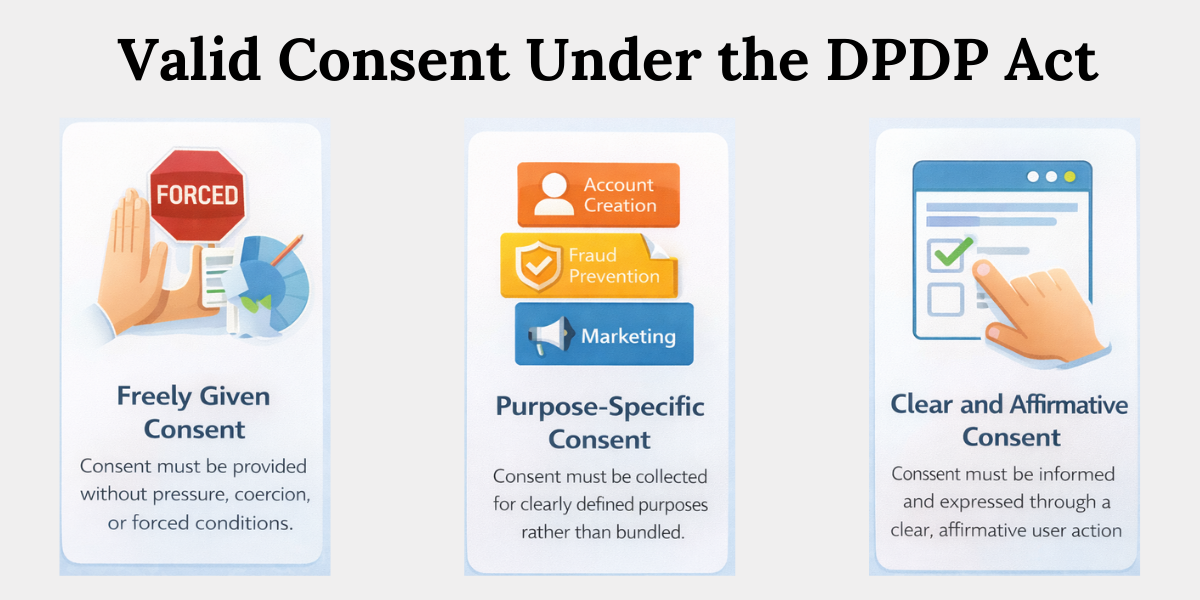
Freely Given Consent
Consent must be provided without pressure, coercion, or forced conditions. For example, users should not be required to accept marketing communications in order to access a service that does not need it, such as completing an online purchase.
Purpose-Specific Consent
Consent must be collected for clearly defined purposes rather than vague or bundled statements. Instead of asking users to agree to generic “data processing,” organizations should provide separate options for purposes like account creation, fraud prevention, marketing communication, or analytics.
Clear and Affirmative Consent
Consent must be informed and expressed through a clear action by the user. Organizations should explain what data is collected and why, and obtain consent through actions such as checking a box or selecting preferences, not through silence or pre-ticked options.
Why Consent Lifecycle Management Matters
Consent lifecycle management ensures that consent remains valid throughout the entire data processing journey, not just at the moment of collection. A robust consent management framework must track consent from collection to withdrawal while ensuring that processing activities respect the original consent boundaries.
Consent behaves like a living permission, not a static document.
The lifecycle typically includes five stages.
1. Consent Collection
The organization collects consent through websites, mobile apps, or digital services.
At this stage, clarity is critical.
Users must clearly understand what they are agreeing to.
2. Consent Recording
The system records the consent event with full context.
This includes purpose tags, timestamps, and consent language versions.
If the organization updates its privacy policy, the new consent version must be recorded separately.
3. Consent Enforcement
Data processing systems must respect consent boundaries.
For example:
If a user declines marketing consent, the CRM system must ensure marketing emails are automatically blocked.
This requires integration between consent management systems and operational platforms.
4. Consent Withdrawal
The DPDP Act requires organizations to provide simple mechanisms for withdrawing consent.
In practice, this means:
- Privacy dashboards
- Preference centers
- Account settings
Withdrawal must be as easy as giving consent.
5. Consent Audit
Organizations must periodically audit consent records and processing activities.
A consent audit typically examines:
- Whether processing purposes match consent records
- Whether withdrawn consent is respected
- Whether legacy data still has valid consent
Without regular audits, consent systems slowly drift out of compliance.
Practical Blueprint for Building a Consent Management Framework
Building a Consent Management Framework requires aligning technology, governance, and regulatory interpretation. Organizations should treat consent management as core compliance infrastructure rather than a simple front-end interface.
Below is a practical roadmap used in many compliance programs.
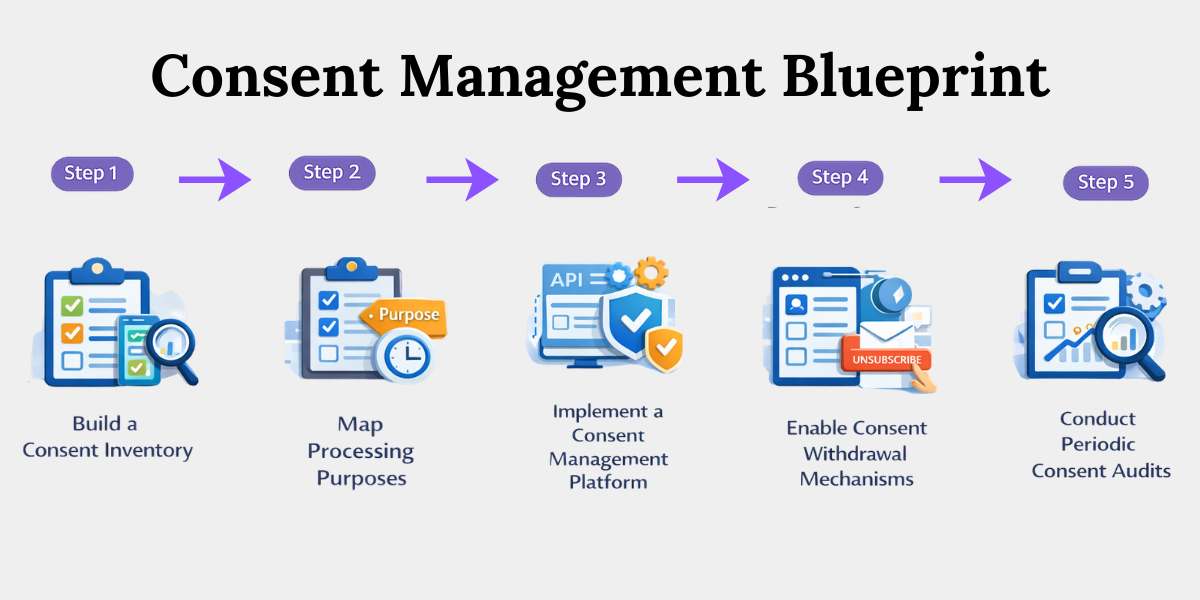
1. Build a Consent Inventory
Start by identifying where consent is collected across the organization.
This often includes:
- Websites
- Mobile applications
- Customer onboarding flows
- Marketing systems
In many organizations, consent exists in multiple disconnected systems.
A consent inventory reveals these silos.
2. Map Processing Purposes
Every consent must correspond to a specific processing purpose.
Create a purpose registry that lists:
- Data category
- Processing purpose
- Legal basis
- Retention period
This becomes the architectural blueprint of your data fortress.
3. Implement a Consent Management Platform
A Consent Management System centralizes consent records and enforces policies.
Typical capabilities include:
- Consent preference dashboards
- API-based consent verification
- Automated consent enforcement
- Consent audit trails
These systems act as the command center of the consent framework.
4. Enable Consent Withdrawal Mechanisms
Users must be able to withdraw consent easily.
Practical options include:
- Privacy preference centers
- Account settings dashboards
- Email unsubscribe mechanisms
Withdrawal signals must propagate across all downstream systems.
5. Conduct Periodic Consent Audits
Compliance is not static.
Organizations should run regular consent audits to verify:
- Consent validity
- Processing alignment
- Withdrawal enforcement
In our observation, many organizations discover during audits that legacy systems still process data based on expired consent.
Conclusion
The DPDP Act fundamentally changes how organizations must manage consent.
Consent is no longer a simple UI element. It is a governance system that must survive regulatory scrutiny.
A well-designed Consent Management Framework functions like a defensive shield inside your data architecture. It records permissions, enforces boundaries, and creates evidence that consent was obtained and respected.
Organizations that invest in robust consent management systems, lifecycle tracking, and auditability will not only achieve compliance with the Digital Personal Data Protection Act 2023 but also build stronger trust with their users.
Because in modern data governance, trust is the strongest compliance strategy.
Key Takeaways
- A consent management framework ensures organizations can collect, manage, enforce, and audit consent in compliance with the DPDP Act.
- Consent must be managed as a lifecycle process, including collection, validation, storage, enforcement, withdrawal, and auditing.
- A consent management system must record how consent was obtained, the purpose of processing, and maintain a verifiable audit trail.
- Consent should be collected through clear, purpose-specific, and affirmative actions rather than vague or bundled consent statements.
- Organizations must maintain detailed consent logs including timestamp, user identity, consent text, purpose, and method of capture.
- Data must only be processed for the specific purposes for which consent was obtained, with systems enforcing these boundaries.
- Valid consent under DPDP must be freely given, purpose-specific, informed, and expressed through a clear affirmative action.
- Organizations should implement consent inventories, purpose mapping, consent platforms, and periodic audits to maintain ongoing compliance.
Related Blog





