Table of contents
March 13, 2026
Privacy by Design and Privacy by Default: Principles of Privacy-First Systems
Privacy failures rarely start with hackers.
They usually start with systems that were never designed with privacy in mind.
Under modern regulations like the Digital Personal Data Protection Act, 2023 and the General Data Protection Regulation, organizations are expected to build privacy safeguards directly into their technology and operations. This requirement is captured through Privacy by Design and Privacy by Default—two foundational principles of modern data protection and privacy-first architecture.
Think of them as the blueprint and automatic defence system of your digital fortress.
One ensures the system is built securely. The other ensures the system behaves securely for users.
What Is Privacy by Design and Privacy by Default?
Privacy by Design and Privacy by Default are principles that require organizations to embed data protection into system architecture and automatically apply privacy-friendly settings for users. Privacy by Design focuses on building secure systems from the start, while Privacy by Default ensures that only the minimum necessary personal data is collected and shared unless users actively choose otherwise.
This concept became globally recognized through GDPR Article 25, which mandates both principles as core compliance obligations.
[Source: GDPR Article 25]
In simpler terms:
- Privacy by Design builds the secure system.
- Privacy by Default activates privacy protection automatically.
Together, they form the operational backbone of modern privacy engineering and compliance frameworks.
Why Privacy by Design and Privacy by Default Matter
Privacy by Design and Privacy by Default are critical for compliance with modern data protection regulations like DPDP and GDPR because they ensure organizations proactively safeguard personal data rather than reacting to privacy failures. These principles help reduce data breaches, enforce accountability, and build trust with users.
The regulatory landscape has shifted dramatically.
Older compliance models focused on documentation and policies. Modern regulations focus on system accountability.
This means regulators now expect organizations to demonstrate:
- How data is collected
- How data is protected
- How data is minimized
- How user rights are enforced
Organizations that treat privacy as a product design principle rather than a legal requirement tend to achieve stronger compliance outcomes.
Why? Because privacy becomes part of daily operations—not just an annual audit exercise.
What Is Privacy by Design?
Privacy by Design is a proactive approach that integrates privacy protections into technology, systems, and business processes from the earliest stages of development. Instead of addressing privacy risks after systems are deployed, organizations design platforms that prevent excessive data collection, restrict access, and secure personal data throughout its lifecycle.
Privacy by Design ensures privacy safeguards exist inside the system itself.
This includes embedding protections such as:
1. Encryption protocols
Encryption protects personal data by converting it into unreadable code that only authorized systems can decode. Even if attackers gain access to the data, the information remains useless without the decryption key.
For example, banking and fintech applications encrypt financial transactions using end-to-end encryption, ensuring that sensitive information such as account numbers and payment details cannot be intercepted during transmission.
2. Secure system design
Secure system design means building software in a way that prevents vulnerabilities before they occur. Developers follow secure coding practices, test systems for weaknesses, and design applications to limit exposure of personal data.
For instance, an e-commerce platform may store customer payment details in separate secure databases, reducing the risk that a single system breach exposes all user information.
3. Access control mechanisms
Access control ensures that only authorized individuals can view or handle personal data. Systems implement role-based access control (RBAC) so employees can only access the information necessary for their job responsibilities.
For example, a customer support employee may see a user’s account activity but cannot access payment card details or internal security logs.
4. Data minimization rules
Data minimization ensures organizations collect only the personal data that is necessary for a specific purpose. This reduces the amount of sensitive data stored within systems and lowers the risk of large-scale breaches.
For example, a newsletter signup form should only require an email address, rather than asking for phone numbers, home addresses, or other unnecessary personal details.
Instead of relying solely on policies, organizations build technical controls that enforce privacy automatically.
In practice, this transforms privacy from a legal document into an operational safeguard.
How Privacy by Design Prevents Data Privacy Risks
Reactive privacy programs fail. Preventive ones work.
Privacy by Design focuses on identifying and mitigating risks before systems go live. Organizations often achieve this through tools such as Privacy Impact Assessments (PIAs).
A Privacy Impact Assessment functions like a structural inspection for digital systems.
It helps organizations identify:
- Unnecessary data collection
- Insecure integrations
- Third-party risks
- Potential regulatory violations
Building Privacy Across the Entire Data Lifecycle
Privacy is not a one-time activity. It follows the entire lifecycle of personal data.
Organizations implementing Privacy by Design typically embed safeguards at every stage.
Lifecycle controls commonly include:
1. Controlled Data Collection
Collect only the personal data that is actually required for a specific purpose. This follows the data minimization principle, which means organizations should avoid collecting excessive or unnecessary information.
For example, if a user signs up for a newsletter, the system should only ask for an email address. Asking for additional details such as phone number, home address, or date of birth would be unnecessary. By limiting data collection, organizations reduce both privacy risks and data breach impact.
2. Secure Processing Mechanisms
Personal data should remain protected while it is being processed inside systems or transferred between services. Organizations achieve this by implementing encryption, tokenization, and secure APIs.
For instance, when a customer makes an online payment, the payment details are encrypted during transmission so that attackers cannot intercept the information. Similarly, tokenization replaces sensitive data such as credit card numbers with random tokens, ensuring the actual data is not exposed during processing.
3. Retention and Deletion Governance
Personal data should not be stored indefinitely. Organizations must establish clear data retention policies that determine how long information should be kept and when it should be deleted.
For example, an e-commerce platform may store purchase records for a few years for accounting purposes, but it should automatically delete inactive user accounts or unused personal data after a defined period. Automated deletion reduces the amount of data stored and lowers the risk of large-scale data breaches.
4. Third-Party Data Protection
Organizations often share personal data with external vendors such as payment processors, cloud providers, analytics services, or marketing platforms. These third parties must also follow strong privacy and security standards.
For example, before integrating a payment gateway or CRM system, a company should conduct vendor due diligence. This may include reviewing the vendor’s security certifications, privacy policies, and data protection practices to ensure they properly safeguard personal data.
When privacy follows the lifecycle, risk exposure drops dramatically.
What Is Privacy by Default?
Privacy by Default requires organizations to configure systems so that the most privacy-protective settings apply automatically. This means personal data collection, visibility, and sharing are restricted to the minimum necessary unless users actively choose otherwise.
In other words, users should not have to hunt for privacy settings.
The safest settings should already be turned on.
Privacy by Default ensures platforms launch with privacy-first configurations.
These configurations typically control:
1. Data visibility
Data visibility determines who can see a user’s personal information within a platform. Privacy by Default ensures that personal information is not publicly visible unless the user chooses to make it visible.
For example, when someone creates a new social media account, their profile details, photos, or contact information should be visible only to approved connections rather than the entire internet. The user can later choose to make certain information public if they want.
This approach prevents accidental exposure of personal data, especially for users who may not understand or modify privacy settings.
2. Behavioural tracking
Behavioural tracking refers to technologies that monitor how users interact with websites or apps, such as browsing habits, clicks, time spent on pages, or purchase behaviour.
Under Privacy by Default, these tracking tools should remain disabled until a user provides clear consent.
For instance, when visiting a website, tracking cookies used for advertising or analytics should not activate automatically. Instead, the website should wait until the user explicitly agrees to them through a consent banner.
This ensures users maintain control over how their online behaviour is monitored and used.
3. Location sharing
Many mobile applications request access to a user’s real-time location data, which can reveal sensitive information such as home addresses, workplaces, or daily routines.
With Privacy by Default, location tracking should be turned off initially. Users should actively enable it only if the feature is necessary.
For example, a ride-hailing or food delivery app may request location access when a user wants to book a ride or track a delivery. However, the app should not continuously track the user’s location in the background without permission.
This protects users from unnecessary location-based profiling or surveillance.
4. Third-party integrations
Many digital platforms connect with external services such as advertising networks, analytics tools, payment providers, or social media plugins.
Privacy by Default ensures that personal data is not automatically shared with these third parties unless it is necessary for the service or the user provides explicit permission.
For example, an e-commerce website may integrate with marketing tools that track user activity for targeted advertising. Under privacy-first settings, this tracking should remain disabled until the user consents to it.
This prevents personal data from being shared across multiple companies without the user’s knowledge or control.
This approach protects users who may never adjust their privacy settings manually.
And realistically, most users never do.
Data Minimization: Collecting Only What Is Necessary
One of the strongest operational outcomes of Privacy by Default is data minimization.
Regulators consistently emphasize that organizations should collect only the personal data necessary for a specific purpose.
In practice, this means limiting:
- Unnecessary registration fields
- Excessive identity verification
- Tracking technologies that collect behavioural data without consent
In our observation, organizations that aggressively collect data create larger breach exposure surfaces.
Less data often means less regulatory risk.
Automatic Privacy Protection Through Default Settings
Privacy by Default works by activating privacy-protective configurations automatically.
Examples include:
-
Tracking Disabled by Default
Websites disable non-essential tracking cookies until users provide explicit consent.
-
Restricted Profile Visibility
User profiles are not publicly visible unless users choose to enable public access.
-
Location Tracking Turned Off
Applications require explicit user action before enabling location sharing.
-
Limited Data Sharing with Third Parties
Personal data is not automatically shared with advertisers or partners.
These measures ensure privacy is built into the user experience—not buried in settings menus.
Why Privacy by Design and Default Are Critical for DPDP Compliance
Privacy by Design and Privacy by Default support the core accountability obligations imposed on organizations under the Digital Personal Data Protection Act (DPDP). These principles help organizations safeguard personal data, enforce consent-based processing, protect children’s data, and respond effectively to data breaches.
Under the Digital Personal Data Protection Act, 2023, organizations acting as data fiduciaries must process personal data responsibly and securely.
This responsibility rests on several operational pillars.
1. Security Safeguards and Breach Protection
Organizations must implement technical safeguards such as:
- Encryption
- Access control
- Network security monitoring
These measures protect personal data from unauthorized access, loss, or misuse.
Strong system architecture—supported by Privacy by Design—plays a crucial role here.
2. Lawful Processing and Consent-Based Data Use
Personal data must only be processed for specific lawful purposes.
This typically requires clear user consent or another valid legal basis.
Privacy by Default helps enforce this by preventing unnecessary data collection before consent is obtained.
3. Safeguarding Children's Personal Data
Many privacy frameworks impose additional safeguards for children’s data.
Organizations must implement stricter controls when handling personal information belonging to minors.
This often includes parental consent mechanisms and restricted data processing.
4. Upholding User Rights and Data Transparency
Modern privacy laws grant individuals the ability to:
- access their personal data
- correct inaccurate information
- request deletion of their data
Privacy-first system design helps organizations implement these rights efficiently.
Without structured data architecture, fulfilling these rights becomes operationally difficult.
Privacy by Design vs Privacy by Default: Key Differences Explained
Privacy by Design focuses on building secure systems and processes, while Privacy by Default governs how privacy settings automatically protect users during everyday system use. Design shapes the architecture of privacy protection, while Default ensures users benefit from those protections without needing to configure them manually.
Many organizations mistakenly treat the two concepts as interchangeable.
They are not.
| Aspect | Privacy by Design | Privacy by Default |
|---|---|---|
| Core Focus | Integrates privacy safeguards into the design and architecture of systems from the beginning. | Ensures that privacy-protective settings are automatically applied when users start using a service. |
| System vs User Settings | Governs how the system is engineered internally. | Governs how the system behaves for users by default. |
| Implementation Stage | Implemented during system design, development, and infrastructure planning. | Applied during product configuration and user interface setup. |
| Operational Scope | Covers the entire data lifecycle, including data collection, processing, storage, and sharing. | Focuses on user-facing settings, such as visibility controls, tracking permissions, and location sharing. |
| Technical Controls | Includes safeguards such as encryption, secure coding practices, privacy impact assessments, and role-based access controls. | Includes privacy-friendly configurations like private profiles, disabled tracking, limited data sharing, and restricted access settings. |
| Responsibility Level | Typically implemented by developers, system architects, and privacy engineers during system development. | Typically implemented through platform settings, product design, and default user configurations. |
| Example | A messaging app stores user conversations using end-to-end encryption and secure servers, ensuring the data is protected within the system. | The same messaging app sets profile visibility to private and disables location sharing by default, so users are automatically protected unless they change the settings. |
Real-World Examples of Privacy by Design and Privacy by Default
Organizations implement Privacy by Design and Privacy by Default through technical safeguards, privacy engineering practices, and user-centric privacy settings. These implementations vary across industries but follow the same goal: reducing unnecessary data exposure and strengthening trust.
Let’s examine how this works in practice.

Fintech Example: Implementing Privacy by Design in Financial Systems
Financial platforms process extremely sensitive personal and financial data.
This makes privacy-first architecture essential.
Typical fintech safeguards include:
-
Secure Coding Practices
Developers follow secure coding standards to prevent vulnerabilities such as injection attacks or insecure data storage.
-
End-to-End Encryption
Financial data remains encrypted both during transmission and while stored in databases.
-
Role-Based Access Control (RBAC)
Employees only access the data necessary for their roles, reducing insider risk.
-
Vendor Risk Assessments
Third-party payment processors and service providers undergo privacy risk evaluations before integration.
These controls ensure financial systems operate like secure digital vaults.
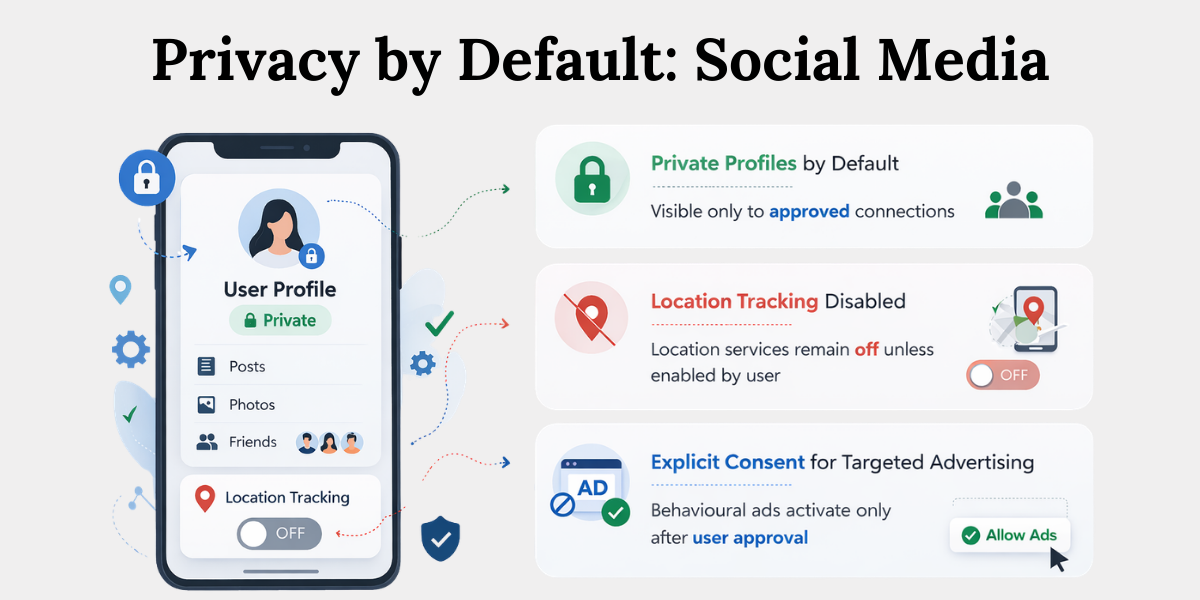
Social Media Example: Implementing Privacy by Default
Social platforms often collect large amounts of personal data.
Without strong default protections, users may unknowingly expose sensitive information.
Typical privacy-first defaults include:
-
Private Profiles by Default
User profiles are visible only to approved connections.
-
Location Tracking Disabled
Location services remain off unless users actively enable them.
-
Explicit Consent for Targeted Advertising
Behavioural advertising only activates after user approval.
These defaults help prevent unintentional privacy exposure.
Why Privacy by Design and Privacy by Default Must Work Together
Privacy by Design and Privacy by Default provide the strongest data protection when implemented together because secure architecture prevents systemic vulnerabilities while default privacy settings protect users during daily system interactions. Organizations that implement only one of these principles often leave critical privacy gaps.
Consider two common failures.
1. Secure Systems Can Still Fail Without Strong Defaults
A platform may have strong encryption and secure infrastructure.
But if user data is publicly visible by default, privacy exposure still occurs.
The architecture is secure.
The configuration is not.
2. Strong Privacy Defaults Cannot Fix Insecure Systems
Now imagine the opposite scenario.
A platform offers privacy-friendly default settings but stores data in unencrypted databases or shares data with unvetted vendors.
In this case, the defaults cannot compensate for weak system design.
Architecture must support privacy.
3. Real Protection Requires Both Design and Default
Organizations that successfully implement modern privacy programs combine both principles.
Their operational model typically includes:
- Designing secure systems from the start
- Applying privacy-friendly default settings
- Conducting continuous privacy risk assessments
- Embedding privacy governance into daily operations
This combined approach creates sustainable and scalable data protection frameworks.
Conclusion
Privacy is no longer just a regulatory requirement.
It is becoming a competitive advantage and a trust signal.
Organizations that adopt Privacy by Design and Privacy by Default build systems that are more secure, more resilient, and easier to regulate. They also reduce the likelihood of data breaches, compliance penalties, and reputational damage.
In a world where personal data powers digital services, privacy must function like invisible infrastructure.
Users should not have to ask whether their data is protected.
The system should already know the answer.
Key Takeaways
- Privacy by Design and Privacy by Default are core principles that embed privacy into system architecture and ensure privacy-friendly settings automatically protect users.
- Privacy by Design focuses on building privacy safeguards such as encryption, secure system design, and access controls directly into technology.
- Preventing privacy risks early is more effective than fixing issues later, which is why organizations assess risks before systems go live.
- Privacy across the data lifecycle ensures protection during data collection, processing, storage, sharing, and deletion.
- Privacy by Default ensures platforms start with the most privacy-protective settings, limiting unnecessary data sharing or tracking.
- Default privacy settings commonly control data visibility, behavioural tracking, location sharing, and third-party integrations.
- Privacy by Design and Privacy by Default serve different roles—one secures the system architecture, while the other protects users through default settings.
- Strong data protection requires both principles together, creating systems that are secure by design and protective by default.
Related Blog
- https://www.privacyglobal.org/blog/what-is-ropa-record-of-processing-activity-dpdp/
- https://www.privacyglobal.org/blog/data-mapping-explained-complete-data-visibility/
- https://www.privacyglobal.org/blog/data-inventory-dpdp-compliance/