Table of contents
April 7, 2026 | 8 min read | DPDP
What is a Data Breach? A Practical Blueprint to Understand, Prevent, and Respond
A data breach is not just a cybersecurity incident. It is a failure of your data protection architecture—where sensitive information is exposed, accessed, or stolen without authorization.
In today’s regulatory climate, a single breach can trigger financial penalties, reputational damage, and legal liability simultaneously.
Most organizations think breaches are rare. They’re not. According to IBM’s Cost of a Data Breach Report, the average global cost reached $4.45 million in 2023, with detection taking over 200 days.
Source: IBM's Cost of a Data Breach Report
So, the real question is not “What is a data breach?”
It’s “Where will your system fail first?”
What is a Data Breach and How Does It Happen?
A data breach occurs when unauthorized access to data leads to the exposure, theft, or misuse of personal data or sensitive information. This can result from cyberattacks, internal negligence, or system misconfigurations, making it both a security failure and a governance failure.
Think of your data as a vault.
A breach doesn’t always mean someone broke the lock. Sometimes, you left the door open.
Where Do Breaches Actually Start? (The Real Entry Points)
1. Misconfigured Systems (The Open Door Problem)
Cloud storage buckets, databases, or APIs are often left publicly accessible due to poor setup. It’s like locking your house but leaving the windows wide open.
Example: A company stores customer data on a cloud server but forgets to restrict public access—anyone with the link can view or download it.
2. Configuration Errors (The Silent Misstep)
Small setup mistakes—wrong permissions, exposed admin panels, or default settings—can quietly create major privacy risks. These errors don’t look dangerous, but they are.
Example: An internal dashboard meant only for employees is accidentally made accessible on the internet without login protection.
3. Phishing Attacks (The Human Firewall Failure)
Attackers trick employees into revealing credentials through fake emails or messages. One convincing email can bypass even the strongest technical defences.
Example: An employee clicks on a “password reset” email that looks legitimate and unknowingly hands over login details to an attacker.
4. Weak Authentication (The Broken Lock)
Relying only on passwords—especially weak or reused ones—makes it easy for attackers to gain access. No second layer means no real barrier.
Example: An employee uses the same password across multiple platforms, and once one site is compromised, attackers gain access to company systems.
5. Unpatched Vulnerabilities (The Cracked Wall)
Outdated software contains known security gaps that attackers actively exploit. Delaying updates is like knowing there’s a hole in your wall and ignoring it.
Example: A company continues using outdated software despite a known vulnerability, allowing attackers to enter using publicly available exploit tools.
Types of Data Breaches
A data breach is not a single event—it is a category of failures, each with distinct causes and regulatory consequences. Understanding the types helps you build targeted defences instead of generic controls.
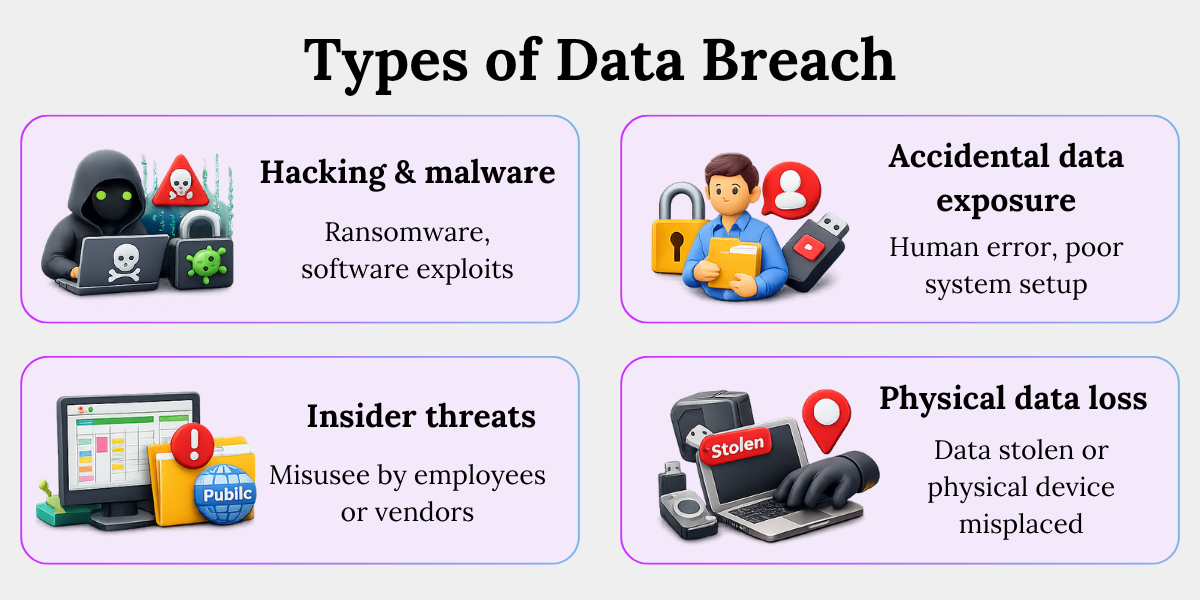
1. Hacking and Malware Attacks (The Forced Entry)
Attackers break into systems using malware, ransomware, or software exploits. This is the classic “break-in” people imagine—but it often requires an existing weakness to succeed.
Example: A ransomware attack encrypts a company’s database, demanding payment to restore access while sensitive customer data is already copied.
2. Insider Threats (The Trusted Risk)
Employees, contractors, or vendors misuse their access—either intentionally or by mistake. The risk comes from having the keys, not breaking the door.
Example: An employee downloads customer data before leaving the company or accidentally shares a confidential file with the wrong external partner.
3. Accidental Data Exposure (The Unintentional Leak)
Data gets exposed due to human error or poor system setup, without any attacker actively involved. These incidents are common because they stem from everyday operations.
Example: A team uploads a spreadsheet with personal data to a shared drive and enables “public access” for convenience, unknowingly exposing it.
4. Physical Data Loss (The Offline Breach)
Sensitive data is lost through stolen or misplaced physical devices like laptops, hard drives, or USBs. Security doesn’t end at digital systems.
Example: An employee’s unencrypted laptop containing customer records is stolen from a cab, exposing all stored data.
What is the Impact of a Data Breach?
A data breach creates multi-layered damage across financial, legal, and operational dimensions. The impact extends far beyond immediate data loss, often affecting long-term business viability and trust.
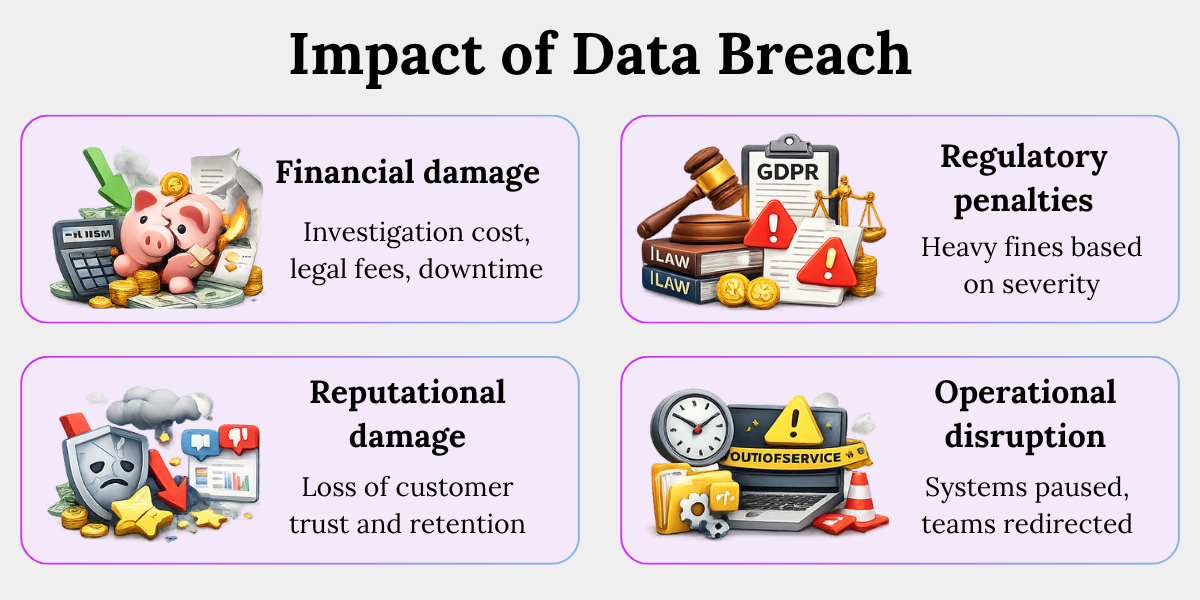
1. Financial Damage (The Immediate Hit)
A data breach directly impacts your bottom line through investigation costs, legal fees, system recovery, and downtime. The average global cost is $4.45 million, and that number rises with delayed detection.
Example: A company spends heavily on forensic audits, legal consultants, and system repairs—while also losing revenue during system outages.
2. Regulatory Penalties (The Legal Shockwave)
Non-compliance with laws like GDPR or the DPDP Act can lead to heavy fines based on revenue and severity of the breach. Regulators assess not just the breach—but how prepared you were.
Example: A company failing to implement basic data protection controls faces penalties because it cannot demonstrate accountability or risk assessment measures.
3. Reputational Damage (The Trust Collapse)
A breach erodes customer confidence, often permanently. Studies show over 60% of customers lose trust after a breach, directly affecting retention and brand value.
Example: Users stop using a platform after their personal data is exposed, choosing competitors they perceive as more secure.
4. Operational Disruption (The Hidden Cost)
Breaches force organizations into crisis mode—systems are paused, teams are redirected, and normal operations slow down or stop entirely. This hidden cost often exceeds initial estimates.
Example: A company halts its services for days to investigate a breach, delaying projects, missing deadlines, and losing business opportunities.
How to Prevent Data Breaches
Preventing a data breach is not about tools. It’s about designing a layered defence system that integrates data security, governance, and accountability.
Build your system like a fortress—not a checklist.
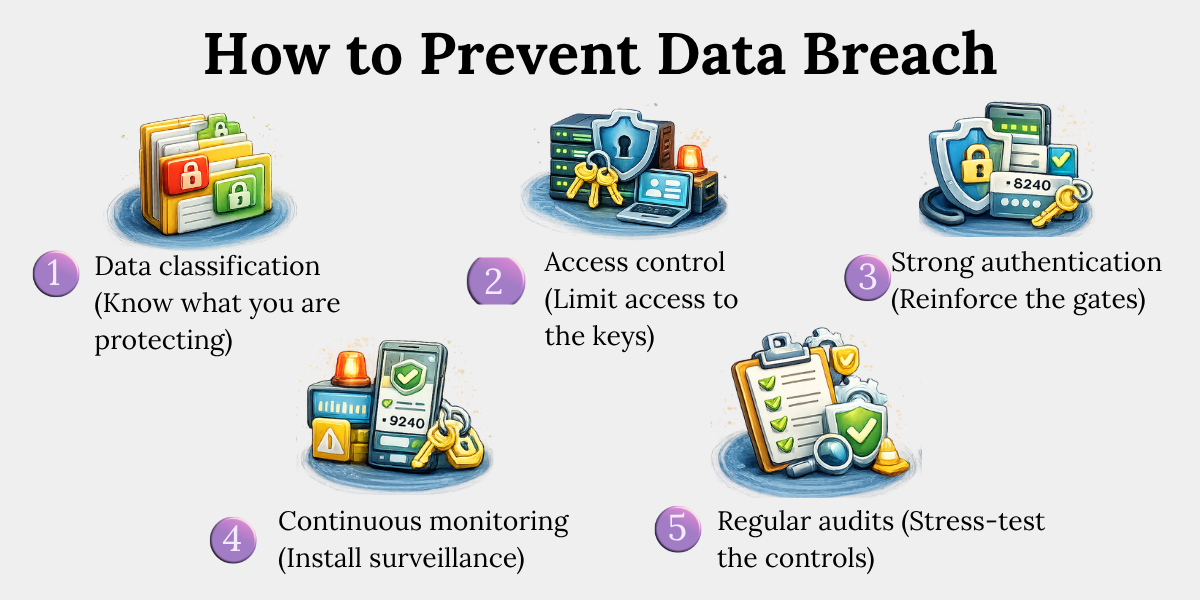
The 5-Layer Data Protection Blueprint
1. Data Classification (Know What You’re Protecting)
Identify and categorize personal data and sensitive information based on risk and importance. Without visibility, protection becomes guesswork.
Example: A company tags customer financial data as “high-risk” and applies stricter controls, while general marketing data gets basic protection.
2. Access Control (Limit the Keys)
Restrict data access using role-based access and least privilege principles—only give access to those who truly need it. More access means more risk.
Example: An HR employee can view payroll data, but a marketing intern cannot—reducing unnecessary exposure.
3. Strong Authentication (Reinforce the Gate)
Implement multi-factor authentication (MFA) to add an extra verification layer beyond passwords. One lock is easy to break; two are not.
Example: Even if an attacker steals a password, they cannot log in without the one-time code sent to the employee’s phone.
4. Continuous Monitoring (Install Surveillance)
Track system activity in real time to detect unusual behaviour before it escalates into a breach. Early detection limits damage.
Example: A system flags a login attempt from a different country at midnight, triggering an alert and blocking access.
5. Regular Audits (Stress-Test the Fortress)
Conduct periodic security audits and vulnerability assessments to identify and fix weak points before attackers do.
Example: An audit reveals outdated software in use, prompting an immediate update before it can be exploited.
Conclusion
A data breach is not an isolated incident. It is a symptom of a weak system design.
You don’t fix breaches after they happen.
You engineer systems where breaches struggle to happen at all.
In our observation, organizations that treat data protection as architecture—not compliance—recover faster, lose less, and build stronger trust.
So, ask yourself:
Is your system a fortress—or just a set of locks?
Key Takeaways
- A data breach happens when sensitive or personal data is accessed without permission.
- Breaches can happen due to hacking, human mistakes, or poor system setup.
- Common causes include misconfigurations, phishing, weak passwords, and outdated software.
- Data breaches can occur in different ways, including cyberattacks, insider actions, accidental exposure, or lost devices.
- They impact money, legal compliance, reputation, and daily business operations.
- Companies often lose money due to recovery costs, downtime, and fines.
- Preventing breaches requires strong controls like limited access, monitoring, and regular checks.
- Good data protection systems help reduce risk and recover faster if a breach happens.
Related Blog





