Table of contents
April 17, 2026 | 9 min read | DPDP
Risk Assessment Decoded
Most businesses don’t fail because of a lack of effort. They fail because they don’t see risk coming—until regulators, hackers, or auditors point it out.
Here’s the uncomfortable truth: if your organization handles personal data, operates digitally, or falls under laws like the DPDP Act, then risk assessment is not optional—it is your first line of defense.
This guide is your practical blueprint. Not theory. Not jargon. Just how to identify, measure, and neutralize data risk, privacy risk, and cybersecurity threats before they become liabilities.
What is Risk?
Risk is the possibility of a negative event occurring that can impact an organization’s data, operations, finances, or legal standing. In a business context, it represents uncertainty—where vulnerabilities, threats, and gaps can lead to data breaches, compliance failures, or operational disruptions if not identified and managed effectively.
Think of risk as unseen pressure on your system.
You may not notice it immediately, but it builds silently—until something breaks.
In data-driven businesses, risk often revolves around:
- Exposure of personal data
- Weak cybersecurity controls
- Non-compliance with regulations like the DPDP Act
Translation: Risk is not the problem. Unidentified risk is.
What is a Risk Assessment?
Risk assessment is a structured process used to identify, analyze, and mitigate risks that could impact an organization’s data, systems, and compliance obligations. It enables businesses to evaluate data risk, privacy risk, and cybersecurity threats, prioritize actions, and implement safeguards to reduce potential harm and ensure regulatory compliance.
Think of it as your early warning system.
You are not just listing risks—you are mapping how your system can fail and building controls to prevent it.
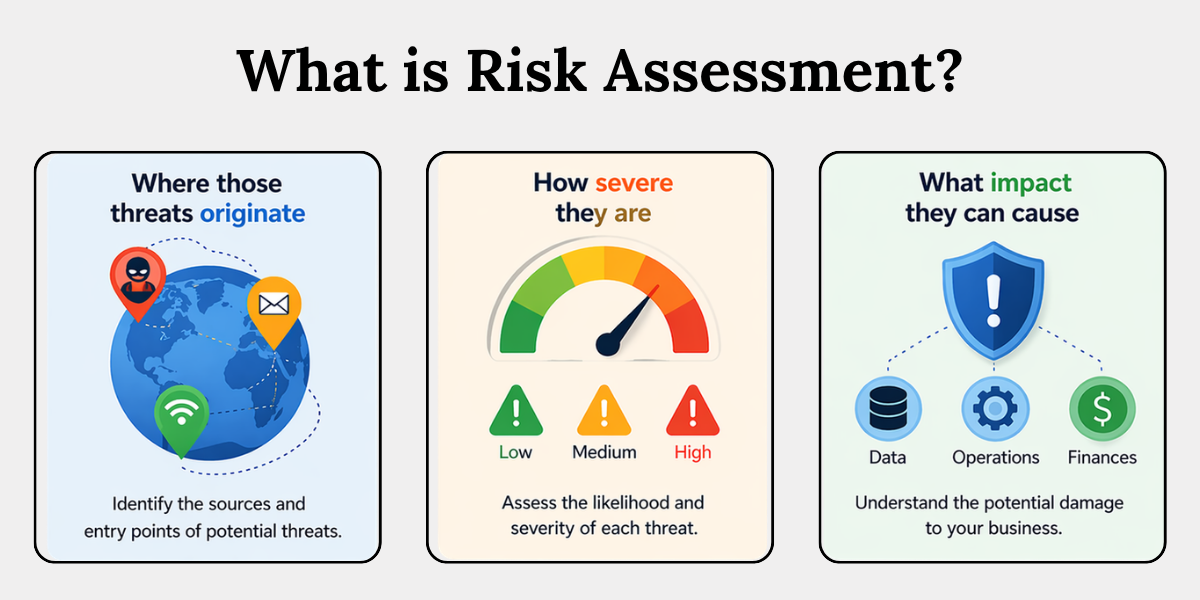
Most businesses operate with partial visibility. They know threats exist but lack clarity on:
- Where those threats originate
- How severe they are
- What impact they can cause
That’s where risk assessment transforms uncertainty into actionable intelligence.
Why Risk Assessment is Critical for Businesses
Risk assessment is essential because it helps organizations prevent data breaches, ensure compliance with laws like the DPDP Act, and protect sensitive personal data from misuse. It enables proactive decision-making, reduces financial penalties, and strengthens cybersecurity resilience across systems and processes.
Let’s be direct. What happens if you skip it?
- You process personal data blindly
- You expose yourself to data breach risk assessment failures
- You fail compliance audits (DPDP, ISO 27001, global laws)
Types of Risk Assessment
Businesses must implement multiple types of risk assessment, including cybersecurity risk assessment, data protection risk assessment, compliance risk management, and operational risk analysis. Each type addresses different exposure areas, ensuring comprehensive protection against technical, legal, and process-level vulnerabilities.
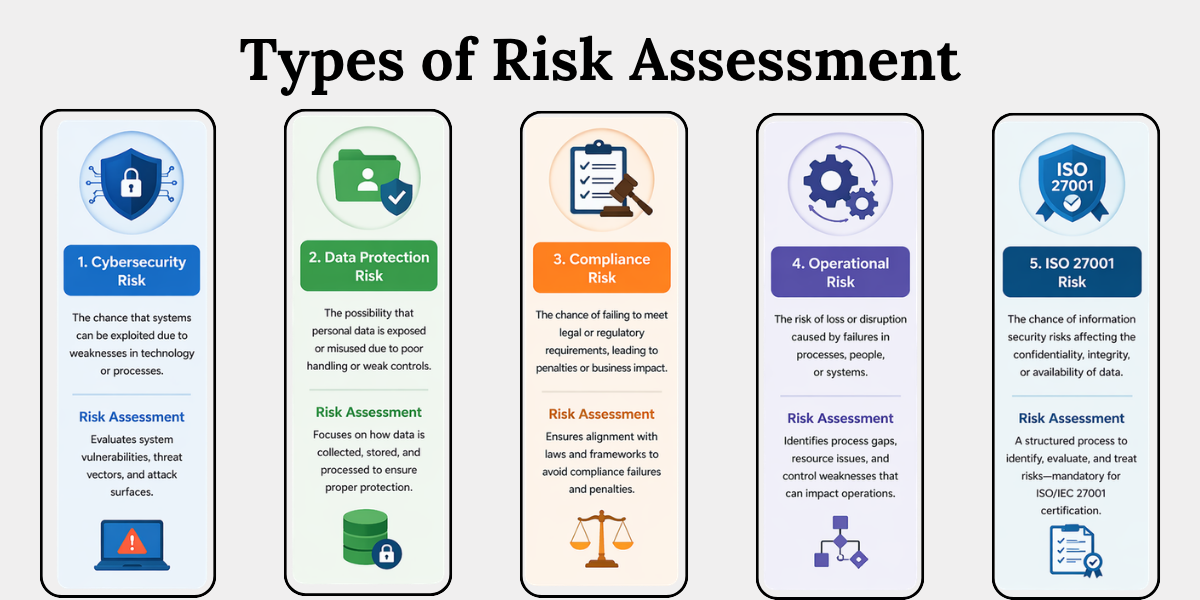
1. Cybersecurity Risk Assessment
Cybersecurity risk is the chance that your systems can be exploited due to weaknesses in technology or processes—in simple terms, where someone can break in.
This evaluates system vulnerabilities, threat vectors, and attack surfaces.
Example: Weak passwords, outdated software, open ports
Focus: Threat and Vulnerability Analysis
Identify:
- Threats → Hackers, malware, insiders
- Vulnerabilities → Weak systems, poor controls
Outcome: Reduced Breach Probability
Fixing vulnerabilities early:
- Limits entry points
- Strengthens defenses
- Reduces chances of data breaches
2. Data Protection Risk Assessment
Data protection risk is the possibility that personal data is exposed or misused due to poor handling or weak controls.
This focuses on how data is collected, stored, and processed.
Example: Unauthorized access to customer databases
Ensures:
- Controlled data access
- Proper storage and handling
- Clear retention policies
It brings structure to how data is managed across the organization.
Critical for DPDP Act Readiness
Without it, businesses risk:
- Unlawful data processing
- Compliance failures
- Increased privacy risk
3. Compliance Risk Management
Compliance risk is the chance of failing to meet legal or regulatory requirements, leading to penalties or business impact.
This ensures alignment with laws like the DPDP Act and global frameworks.
Example: Missing consent mechanisms
Non-compliance can lead to:
- Financial penalties under laws like the DPDP Act
- Loss of customer trust
- Operational disruptions
Compliance risk quickly becomes business risk.
4. ISO 27001 Risk Assessment
ISO/IEC 27001 is a global standard for managing information security through structured risk management.
ISO requires a formal risk assessment process.
Includes: Identification, Evaluation, and Treatment
- Identify risks (assets, threats, vulnerabilities)
- Evaluate impact and likelihood
- Treat risks using controls or mitigation plans
Mandatory for Certification
To get certified:
- You must document your risk assessment
- Show how risks are handled and monitored
No risk assessment = no certification.
How to Do a Risk Assessment?
To perform a risk assessment, businesses must identify assets, detect threats and vulnerabilities, analyze risk impact, prioritize risks, implement mitigation controls, and continuously monitor outcomes. This structured process ensures effective data risk management and compliance with cybersecurity and privacy standards.
Let’s break it down into actionable steps:
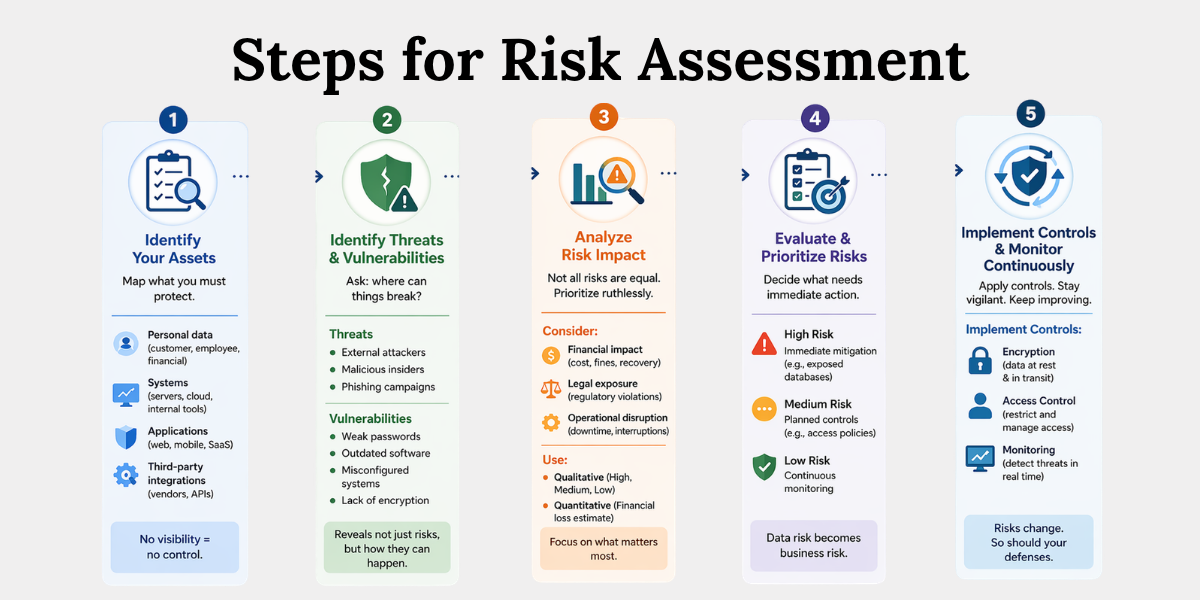
Step 1: Identify Your Assets
Map what you must protect.
Start by identifying all critical assets within your organization—not just obvious ones like databases, but anything that stores or processes value.
This includes:
- Personal data (customer records, employee data, financial details)
- Systems (servers, cloud environments, internal tools)
- Applications (web apps, mobile apps, SaaS platforms)
- Third-party integrations (vendors, APIs, outsourced processors)
If you don’t know what you have, you cannot protect it.
No visibility = no control.
Step 2: Identify Threats and Vulnerabilities
Ask the uncomfortable question: where can things break?
Once assets are identified, assess what could go wrong and where your weaknesses lie.
- Threats → External attackers, malicious insiders, phishing campaigns
- Vulnerabilities → Weak passwords, outdated software, misconfigured systems, lack of encryption
For example, a customer database may be secure—but if employee access controls are weak, it becomes an entry point.
This step is your threat and vulnerability analysis layer—it reveals not just risks, but how they can actually occur.
Step 3: Analyze Risk Impact
Not all risks are equal. Prioritize ruthlessly.
Every identified risk must be evaluated based on its potential impact on the business.
Consider:
- Financial impact → Cost of breach, fines, recovery expenses
- Legal exposure → Violations under laws like the DPDP Act
- Operational disruption → Downtime, service interruptions
Organizations typically use:
- Qualitative models → High, medium, low risk ratings
- Quantitative models → Financial value of potential loss
The goal is simple: separate critical risks from background noise.
Step 4: Risk Evaluation & Prioritization
Decide what needs immediate action.
After analyzing impact and likelihood, categorize risks to determine response urgency.
- High risk → Immediate mitigation (e.g., exposed databases)
- Medium risk → Planned controls (e.g., improving access policies)
- Low risk → Continuous monitoring
For instance, a vulnerability exposing personal data is far more urgent than a minor internal process gap.
This is where data risk becomes business risk, influencing decisions at the leadership level.
Step 5: Implement Controls
Once risks are prioritized, apply appropriate controls to reduce or eliminate them.
Common controls include:
- Encryption → Protect data at rest and in transit
- Access control → Restrict who can view or modify data
- Monitoring systems → Detect suspicious activity in real time
These controls should align with recognized frameworks like ISO 27001 risk treatment plans, ensuring consistency and audit readiness.
Controls turn insights into action—they are your actual line of defense.
Step 6: Continuous Monitoring
Risk assessment is not a one-time exercise. Systems evolve, threats change, and new vulnerabilities emerge.
Ongoing practices include:
- Regular audits → Reassess risks periodically
- System updates → Patch vulnerabilities and upgrade defenses
- Policy reviews → Ensure compliance with evolving regulations
For example, a secure system today may become vulnerable tomorrow due to a new exploit.
Continuous monitoring ensures your defenses stay relevant, updated, and effective over time.
Why Businesses Need Professional Risk Assessment Services
Professional risk assessment services provide expert-led analysis, standardized frameworks, and compliance-aligned strategies to identify and mitigate risks effectively. They help businesses meet cybersecurity, data protection, and ISO certification requirements while ensuring continuous monitoring and improvement.
At Privacy Global, we help you move from uncertainty to control—designing risk frameworks that align with your business, regulatory obligations, and growth plans.
Because effective risk assessment isn’t just about finding gaps—it’s about building systems that don’t fail.
Conclusion
Risk doesn’t announce itself. It exploits silence, gaps, and assumptions.
Risk assessment is your blueprint, your shield, and your early warning system. Without it, you’re not managing compliance—you’re gambling with it.
The smartest organizations don’t wait for breaches or penalties.
They build systems that prevent them.
Now the real question is:
Are you identifying your risks—or discovering them too late?
Key Takeaways
- Risk is the chance of harm to data, systems, or compliance.
- Risk assessment helps identify and reduce cybersecurity, data, and privacy risks.
- It is essential for protecting personal data and meeting laws like the DPDP Act.
- Different types cover cybersecurity, data protection, compliance, and ISO standards.
- Cybersecurity risk looks at system weaknesses and threats.
- Data protection risk focuses on how personal data is handled.
- A step-by-step process helps manage and reduce risks effectively.
- Expert services help businesses stay compliant and secure.
Related Blog