Table of contents
April 24, 2026
Data Breach Response: What to Do After a Data Breach?
Most organizations don't fail compliance-they fail response.
A breach happens in minutes. Confusion lasts for weeks.
Under the Digital Personal Data Protection Act (DPDP Act), the real risk isn't just the
breach-it's what you do next. Regulators don't expect perfection. They expect
preparedness, speed, and accountability.
But here's the catch:
You can't build a response plan if you don't fully understand what you're responding to.
Before we break down a data breach response, we need to start at the
foundation-what exactly is a data breach?
What is a Data Breach?
A data breach is any unauthorized access, disclosure, alteration, or loss of
personal data, whether accidental or intentional. Under the DPDP Act, even a minor
exposure-like sending personal data to the wrong recipient-can qualify as a breach
and trigger compliance obligations.
Think of it this way:
If personal data escapes your control-even briefly-you're in breach territory.
We've covered this in detail, including types and real-world examples.
👉 Learn more about data breach here
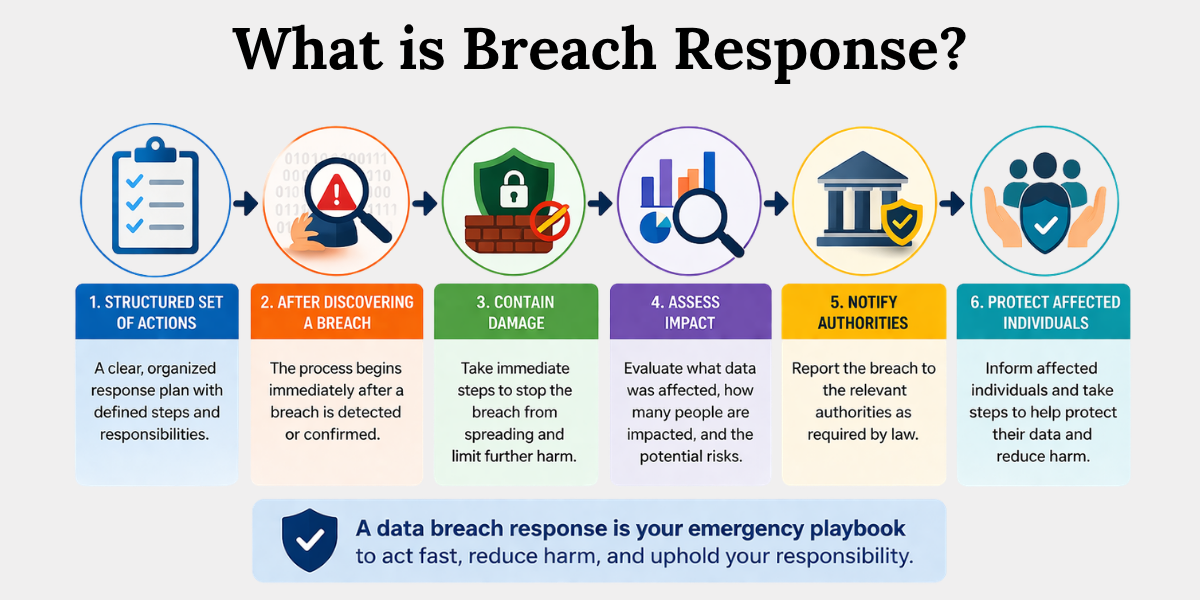
What is a Data Breach Response?
A data breach response is a structured set of actions an organization must take
immediately after discovering a breach to contain damage, assess impact, notify
authorities, and protect affected individuals. Under the DPDP Act, this is not
optional-it is a legal obligation tied to data fiduciary duties.
In simple terms:
This is your emergency playbook when your data fortress is breached.
What to Do After a Data Breach?
A compliant data breach response under DPDP Act requires organizations to act
quickly to contain the breach, assess its impact, notify the Data Protection Board of
India, inform affected individuals, and implement corrective measures. The law
emphasizes timely reporting and accountability, making delay one of the biggest
compliance risks.
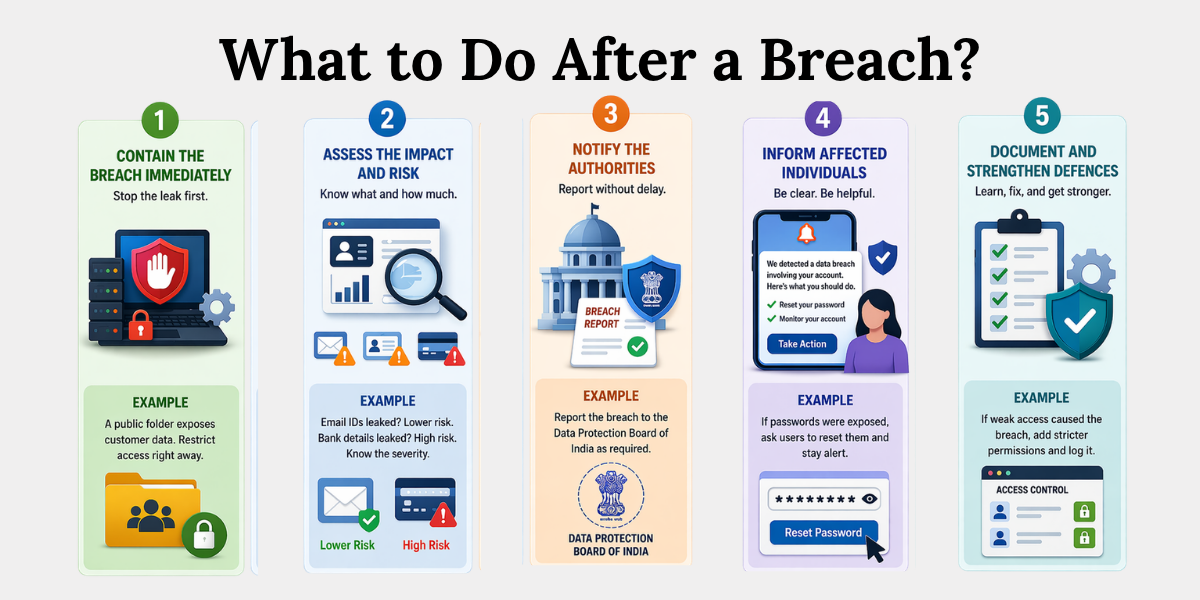
Think of this as your 5-layer defence system-each layer must activate immediately.
1. Contain the Breach Immediately
Stop the leak first. Don't overthink it.
As soon as you detect a breach, block access to the affected system. This could
mean disabling a server, revoking login access, or fixing a misconfiguration.
For example, if customer data is accidentally made public on a shared drive, restrict
access immediately.
Every minute of delay can expose more data.
2. Assess the Impact and Risk
Figure out what was exposed and how serious it is.
Check what type of data was leaked and how many people are affected. Basic data
like names is lower risk, but financial or ID data increases the severity.
For instance, a leak of email IDs is manageable. A leak of bank details is a serious
compliance issue.
This step decides how urgent your response needs to be.
3. Notify the Authorities (DPDP Requirement)
Inform regulators before the situation escalates.
Under the DPDP Act, you must report the breach to the Data Protection Board of
India without delay.
Companies often wait to "confirm everything"-that's a mistake.
Delayed reporting can create bigger legal problems than the breach itself.
4. Inform Affected Individuals
Tell users clearly what happened and what they should do.
Explain the breach in simple terms and guide them on next steps.
For example, if passwords are exposed, ask users to reset them immediately.
Clear communication reduces panic and builds trust.
5. Document and Strengthen Your Defences
Record everything and fix the gap.
Document what happened, how you handled it, and what changes you made. This
helps in audits and prevents repeat issues.
For example, if weak access control caused the breach, implement stricter
permissions.
A good response doesn't just fix the issue-it improves your system.
Best Practices for an Effective Breach Response Plan
An effective data breach response plan under the DPDP Act is built before a breach
occurs-not during it. Organizations must define clear processes, assign
accountability, and continuously test their response systems to reduce reaction time
and ensure compliance.
Think of this as building your compliance fortress before the attack happens.
1. Define a Clear Response Team
Assign roles across legal, IT, and compliance teams. Everyone should know their
responsibility the moment a breach is detected. Without defined ownership, response
delays are inevitable.
2. Create a Documented Response Playbook
Build a standardized breach response protocol covering detection, reporting, and
communication. This ensures consistency and prevents ad-hoc decision-making under
pressure.
3. Implement Real-Time Detection Systems
Use monitoring tools to detect anomalies early. The faster you detect a breach, the
lower the impact-and the stronger your compliance position.
4. Conduct Regular Breach Simulations (Drills)
Run mock breach scenarios to test your team's readiness. Think of it as a fire drill for
your data systems-ignored until needed, but critical when it matters.
5. Maintain Detailed Audit Trails
Keep structured records of incidents and responses. Regulators rely on documentation
to assess compliance, not verbal explanations.
6. Continuously Update Security Safeguards
Post-breach fixes are not enough. Regularly audit and upgrade your systems to prevent
repeat incidents.
Conclusion
The DPDP Act doesn't just test your systems-it tests your ability to respond under
pressure.
And here's the reality: most organizations don't fail because of the breach-they fail
because of the response.
You don't build a defence system during an attack. You build it before.
Treat your data breach response as a core compliance architecture-not a reactive
checklist.
Because in today's regulatory environment, your response is your strongest
defence-or your biggest liability.
Key Takeaways
- Under the DPDP Act, the real risk is not the breach itself, but how effectively you
respond to it. - A data breach occurs whenever personal data escapes your control, even due to
simple mistakes like sharing it with the wrong person. - A data breach response is a mandatory, structured action plan that every data
fiduciary must follow after a breach. - An effective response starts with quickly containing the breach to stop further
data exposure. - Assessing the type of data and impact helps determine the urgency and
seriousness of the breach. - Organizations must notify the Data Protection Board of India without delay to
remain compliant under the DPDP Act. - Clear communication with affected individuals helps reduce panic and maintain
trust. - A strong breach response plan is built in advance through defined roles,
systems, and regular testing-not during a crisis.
Related Blog
- https://www.privacyglobal.org/blog/what-is-data-breach
- https://www.privacyglobal.org/blog/data-subject-access-request-dsar-explained
- https://www.privacyglobal.org/blog/what-is-risk-assessment





