Table of contents
April 28, 2026
Is Data Security Enough for DPDP Compliance?
Most businesses believe that if their data security is strong, they are automatically compliant with the Digital Personal Data Protection Act (DPDP Act).
That assumption is not just incorrect—it creates serious compliance risks.
Data security protects data. DPDP compliance governs how you are allowed to collect, use, and manage it.
You can build a highly secure system… and still violate the law.
What Is Data Security?
Data security refers to the technical and organizational measures used to protect data from unauthorized access, breaches, or loss. It focuses on safeguarding systems, networks, and databases through controls like encryption, access management, and monitoring.
Think of data security as your fortress—it keeps attackers out. But it doesn’t decide whether you should have collected the data in the first place.
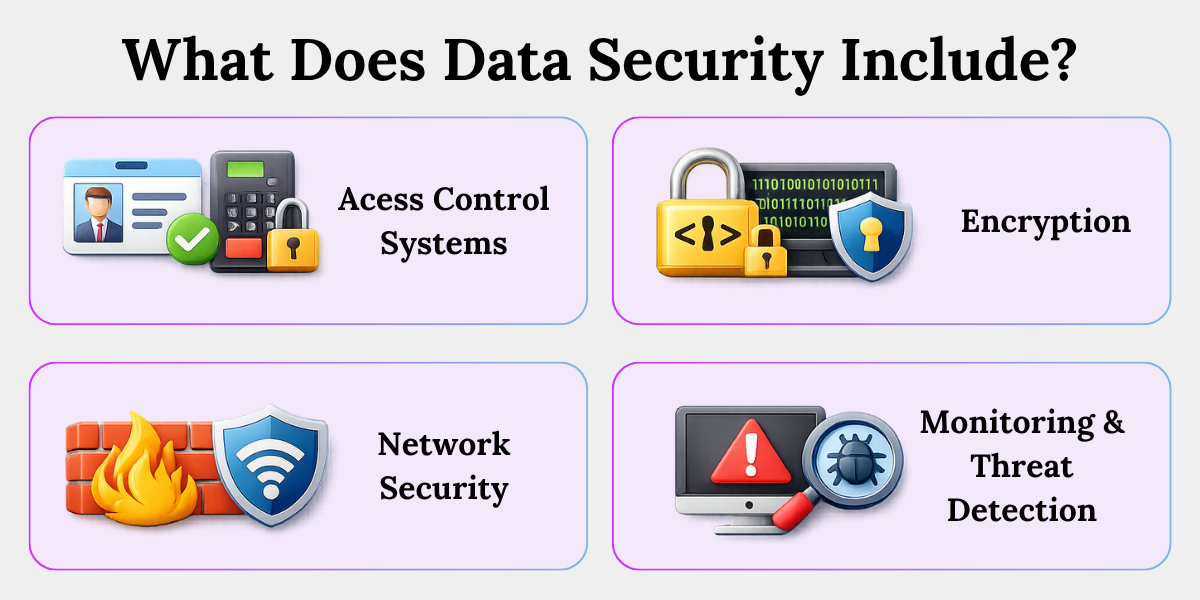
What Data Security Covers
1. Access Control Systems
This decides who can see or use specific data.
Example: In a company, only the HR team can access employee salary details. Interns or unrelated teams cannot view this information. This reduces the risk of internal misuse.
2. Encryption (Data at Rest & in Transit)
This converts data into unreadable code so that even if someone steals it, they cannot understand it.
Example: When you enter your password on a website, it is encrypted so hackers cannot read it even if intercepted.
3. Network Security (Firewalls, IDS/IPS)
These systems act like guards at the entry points of your system, blocking unauthorized access.
Example: A firewall prevents unknown or suspicious IP addresses from accessing your company’s database.
4. Monitoring & Threat Detection
This involves continuously watching systems for unusual activity.
Example: If someone tries to log in multiple times with the wrong password, the system flags it or blocks access.
Key Insight: Data security focuses on protecting data from threats—not on whether you are using that data legally.
What Is DPDP Compliance Under the DPDP Act?
DPDP compliance means following the legal rules set under the Digital Personal Data Protection Act for collecting, processing, and managing personal data. It ensures that organizations handle data responsibly, transparently, and with user consent.
This is your legal shield.
Under the law, businesses (called data fiduciaries) are responsible for how they handle personal data—not just how securely they store it.
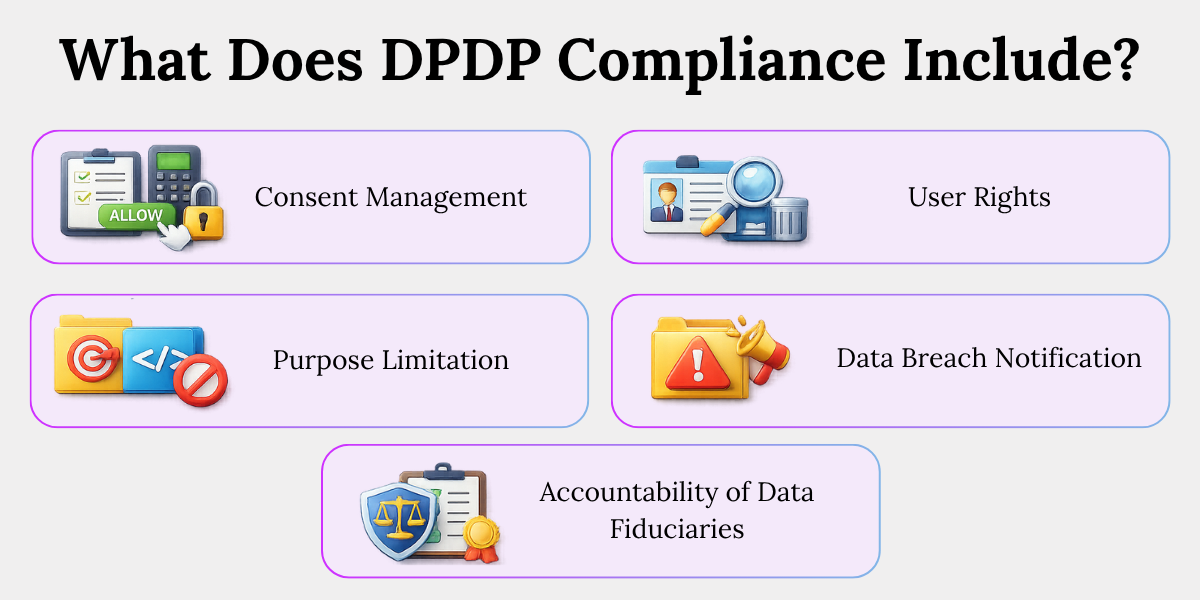
What DPDP Compliance Includes
1. Consent Management
You must clearly ask users for permission before collecting their data.
Example: When a website asks, “Do you agree to share your email for updates?”—that is consent. Without this, collecting the email is not allowed.
2. Purpose Limitation
You can only use data for the reason you originally told the user.
Example: If a user shares their phone number for order delivery, you cannot later use it for marketing calls without separate consent.
3. User Rights (Data Principals)
Users have the right to access, correct, or delete their data.
Example: A user can request a company to delete their account and all associated data—and the company must comply.
4. Data Breach Notification
If a data breach happens, you must inform authorities and affected users.
Example: If customer data is leaked, the company cannot hide it—it must disclose it.
5. Accountability of Data Fiduciaries
The business is responsible for ensuring all rules are followed.
Simple meaning: You are legally answerable for how you handle user data.
Key Insight: DPDP compliance focuses on lawful and fair use of data—not just protection.
Is Data Security Enough to Ensure DPDP Compliance in India?
No, data security alone is not enough to ensure DPDP compliance in India. While security protects data from breaches, DPDP compliance requires lawful collection, valid consent, purpose limitation, and user rights—none of which are guaranteed by technical safeguards alone.
This is the core misunderstanding.
You might have:
- Strong encryption
- Secure servers
- Advanced cybersecurity tools
And still be non-compliant.
Why? Because security does not address legality or user rights.
What Data Security Does NOT Cover
1. Consent Collection
Data security does not ensure that you asked for permission before collecting data.
Example: You may securely store email IDs, but if users never agreed to share them, you are violating the law.
2. Purpose Limitation
Security does not restrict how you use data.
Example: Even if data is secure, using it for a different purpose than originally stated is non-compliant.
3. User Rights Enablement
Security systems do not automatically allow users to access or delete their data.
Example: A secure database may store data safely, but if users cannot request deletion, you are non-compliant.
4. Regulatory Accountability
Technical systems do not ensure you meet legal obligations.
Example: Having firewalls does not prove that you are following DPDP rules.
Blunt truth: You can securely manage data that you were never legally allowed to collect or use.
What Does Data Security Cover vs What DPDP Compliance Requires?
Data security focuses on protecting data through technical controls, while DPDP compliance ensures that personal data is collected and used lawfully. Security is about protection; compliance is about permission, responsibility, and rights.
Here’s the difference in simple terms:
| Aspect | Data Security (What it Covers) | DPDP Compliance (What it Requires) |
|---|---|---|
| Core Focus | Keeps data safe from hackers or unauthorized access | Ensures data is collected and used legally |
| Nature | Technical systems and tools | Legal rules and responsibilities |
| Main Goal | Prevent data breaches | Protect user rights and ensure fair use |
| Example | Encrypting user passwords so no one can read them | Taking user consent before collecting those passwords |
| Control Type | Firewalls, access control, monitoring tools | Consent forms, privacy policies, user rights processes |
| Key Question | “Can this data be protected?” | “Are we allowed to collect and use this data?” |
Simple Way to Understand
- Data Security = Locking your house properly
- DPDP Compliance = Having the legal right to own and use what’s inside the house
Both are important—but they solve completely different problems.
Conclusion
Businesses must treat data security and DPDP compliance separately because they address two fundamentally different risks—technical threats and legal violations.
Data security ensures that your systems are protected from breaches. But DPDP compliance ensures that your entire approach to handling personal data is lawful, transparent, and accountable.
If you focus only on security:
- You may protect data from hackers
- But still misuse it legally
If you focus only on compliance:
- You may follow legal processes
- But leave systems vulnerable to attacks
That is why both must exist together—but never be confused as the same thing.
Final Thought:
Data security protects the data you have.
DPDP compliance questions whether you should have that data at all.
Key Takeaways
- Data security protects data from breaches, not how it is legally used.
- DPDP compliance ensures personal data is collected, processed, and used lawfully.
- Strong data security alone does not make a business DPDP compliant.
- Data security covers technical measures like access control, encryption, and monitoring.
- DPDP compliance includes consent, purpose limitation, user rights, and accountability.
- Data security does not ensure consent, lawful use, or user rights.
- Data security focuses on protection, while DPDP compliance focuses on legality.
- Both are essential but fundamentally different and must be implemented together.
Related Blog
- https://www.privacyglobal.org/blog/what-is-data-breach
- https://www.privacyglobal.org/blog/data-privacy-myths-debunked
- https://www.privacyglobal.org/blog/ai-and-privacy-how-ai-uses-personal-data





