Table of contents
March 3, 2026
Why DPDP Compliance Matters to Government Sector?
Government data is not just information.
It is sovereign infrastructure.
Under the DPDP Act, 2023, every ministry, PSU, public company, and statutory body that determines the purpose and means of processing personal data is a data fiduciary. That includes the entire government sector unless specifically exempted under law.
The era of assumed immunity is over. The era of accountable architecture has begun.
This is not a policy debate. It is an operational shift.
Let’s build the blueprint.
Does the DPDP Act Apply to Government Bodies in India?
Yes. The DPDP Act applies to government bodies when they process digital personal data, unless a specific exemption is notified under Section 7 or other enabling provisions. Government departments, PSUs, and public companies can qualify as data fiduciaries or even significant data fiduciaries depending on scale, risk, and volume of sensitive data processed.
The assumption that “government is automatically exempt” is inaccurate.
The DPDP Act defines a data fiduciary as any person — including the State — who determines the purpose and means of processing personal data.
Translation? If you decide why data is collected, you carry statutory responsibility.
Are Government Departments Exempt Under the DPDP Act?
Government departments may receive limited exemptions under Section 7 or through specific notifications for sovereignty, security, or public order purposes. However, these exemptions are conditional shields — not blanket immunity. Core obligations like reasonable security safeguards and breach response may still apply.
Exemption is not invisibility.
It is a policy-controlled shield. And shields come with limits.
Government departments may receive limited and purpose-specific exemptions under the DPDP Act, particularly for sovereignty, national security, public order, and prevention of offences.
However, exemptions are conditional and notification-based — not automatic or blanket protections.
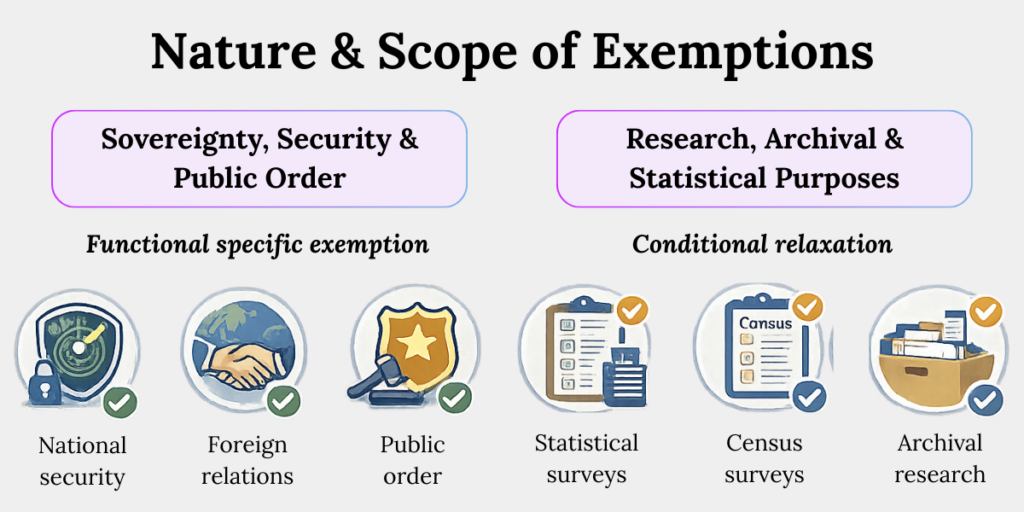
Nature and Scope of Exemptions
It documents:
1. Exemptions for Sovereignty, Security & Public Order
The Central Government may exempt certain processing activities where disclosure could affect national security, foreign relations, public order, or prevention of offences.
This typically applies to intelligence agencies, law enforcement bodies, or strategic ministries.
However, exemption applies only to specific functions — not the entire department.
2. Exemptions for Research, Archival & Statistical Purposes
Government bodies engaged in statistical surveys, census operations, or archival research may receive conditional relaxation, provided appropriate safeguards are implemented.
The exemption does not remove security obligations — it modifies consent or notice requirements in defined scenarios
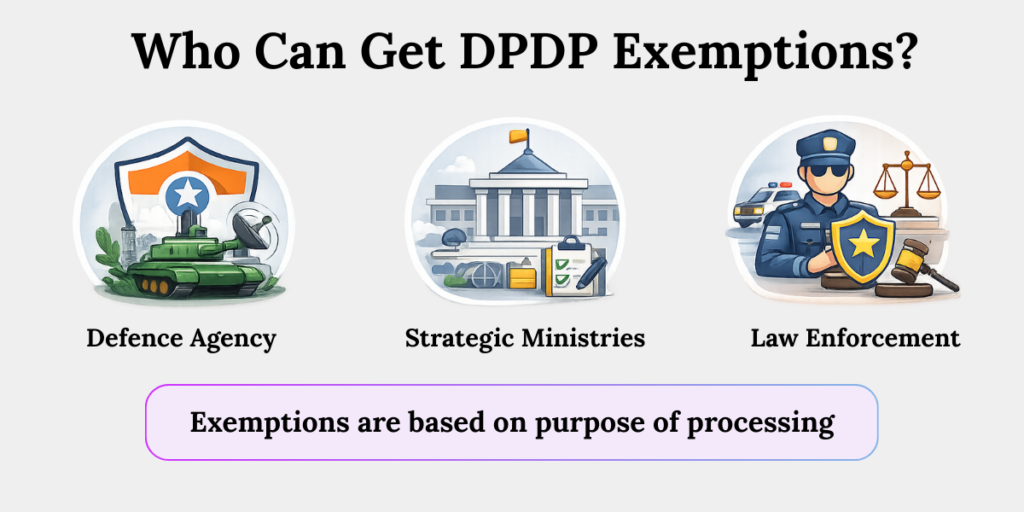
Who Can Receive Exemptions?
1. Notified Agencies or Departments
Exemptions are granted through formal notification. Ministries handling defence intelligence or strategic surveillance may qualify — but only for defined processing categories.
Routine HR data, pension databases, procurement systems, or welfare registries do not automatically qualify.
2. Function-Specific Processing Activities
The exemption is tied to the purpose of processing, not the identity of the entity.
For example, a law enforcement unit may be exempt while investigating national security threats, but its payroll department remains fully accountable as a data fiduciary.
Why DPDP for Government Sector Is a Structural Risk Issue
DPDP for government matters because public sector entities process large-scale personal data and sensitive data — including Aadhaar-linked records, health databases, welfare data, tax records, and citizen registries. High-volume processing increases classification risk as a Significant Data Fiduciary and amplifies breach liability exposure.
India hosts over 1.4 billion residents and one of the world’s largest digital public infrastructures. The government sector is the largest centralized processor of citizen data in the country.
More scale. More exposure.
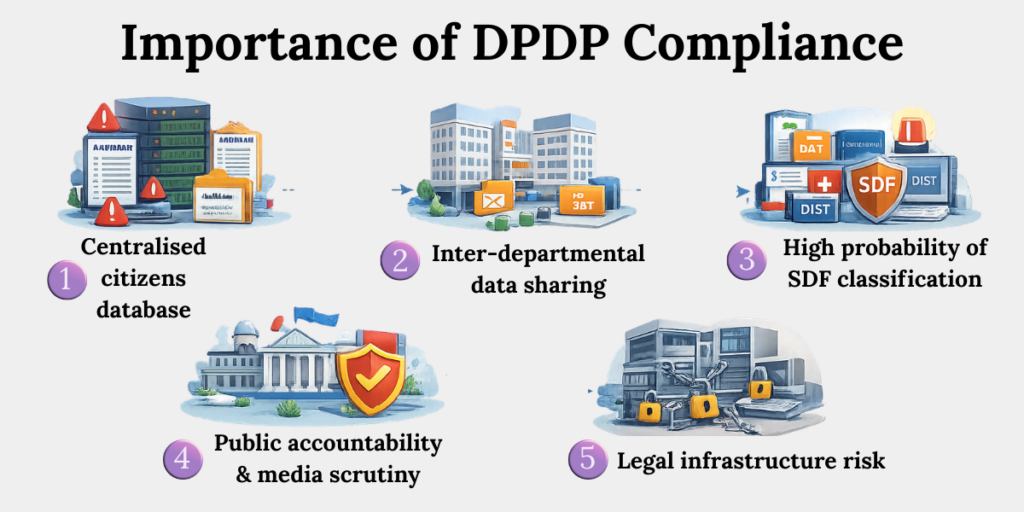
1. Centralized Citizen Databases
Government bodies maintain large, aggregated databases — Aadhaar-linked welfare records, tax filings, land registries, health records. A single vulnerability can expose millions of data principals, creating systemic trust and governance risk.
2. Inter-Departmental Data Sharing
Data frequently flows between ministries, state departments, and public companies. Without defined data-sharing agreements and purpose limitation controls, processing becomes opaque — increasing fiduciary liability.
3. High Probability of Significant Data Fiduciary Classification
Large schemes like DBT, public health insurance, or digital education initiatives may trigger SDF designation due to scale and sensitivity. Enhanced compliance obligations increase operational complexity.
4. Public Accountability & Media Scrutiny
Unlike private companies, government breaches become parliamentary questions and media headlines. Regulatory non-compliance translates into political and administrative consequences.
5. Legacy Infrastructure Risk
Many government systems operate on legacy IT architecture with fragmented access controls. DPDP compliance requires modernization of governance, not just policy circulars.
Structural risk means compliance cannot be departmental.
It must be architectural.
Under the DPDP Rules, data fiduciaries must implement:
- Reasonable security safeguards
- Breach notification within 72 hours
- Record maintenance
- Grievance redressal mechanisms
Now ask yourself.
Is your department architected for that level of accountability?
Can a Government Body Be a Significant Data Fiduciary?
A government entity may be designated as a Significant Data Fiduciary (SDF) based on volume, sensitivity, risk to rights of data principals, or impact on electoral democracy and national security. Such designation triggers enhanced obligations like DPIA, independent audits, and Data Protection Officer appointments.
Large welfare schemes. Health registries. Education databases. These are high-risk processing ecosystems.
In practical terms, classification as an SDF carries following obligations:
1. Mandatory Data Protection Officer
A government-designated Significant Data Fiduciary must appoint a qualified DPO based in India.
For a PSU bank or digital welfare authority, this means creating an independent oversight role reporting to senior leadership — not embedding compliance within IT or legal alone.
2. Periodic data audits
Independent audits must assess technical and organizational measures.
For example, a public health authority handling vaccination records would need third-party audit validation of encryption standards, access logs, and vendor data processing practices.
3. Data Protection Impact Assessments (DPIA)
Before launching large digital initiatives — such as a centralized beneficiary portal — the department must conduct DPIA to evaluate risks to data principals.
This includes profiling risks, automated decision-making impacts, and potential misuse scenarios.
4. Enhanced reporting standards
SDFs face higher reporting and documentation expectations.
Ministries managing nationwide platforms must maintain detailed processing records, risk assessments, and incident reports that withstand regulatory scrutiny.
SDF status increases accountability depth.
It demands governance maturity.
What Are the DPDP Compliance Obligations for Government Sector?
Government data fiduciaries must provide clear notices, obtain valid consent (where applicable), implement security safeguards, notify breaches, respect data principal rights, and erase personal data once purpose is fulfilled unless retention is legally required.
[Source: DPDP Act & DPDP Rules]
Let’s break this into an actionable defence architecture.
1. Classify Data Assets
Conduct structured data mapping across ministries, PSUs, and govt bodies. Identify legal basis, purpose specification, retention mandates under allied laws (e.g., RTI, tax statutes), and cross-border data exposure.
Fragmented databases without documented processing logic create audit vulnerabilities.
2. Strengthen Security Safeguards
Implement encryption-at-rest, role-based access control (RBAC), centralized log monitoring, and incident detection systems aligned with CERT-In advisories.
Government networks require layered defence architecture, especially where citizen-facing portals interface with backend systems.
Security is governance. Not a procurement checklist.
3. Build Breach Notification Protocol
Design escalation matrices to notify the Data Protection Board within prescribed timelines.
Ministries must predefine internal response chains — IT → Legal → Secretary-level escalation — to prevent procedural delay during cyber incidents.
Delay is not procedural error. It is statutory exposure.
4. Enable Data Principal Rights
Establish digital grievance portals for access, correction, and erasure requests.
For example, a municipal corporation managing property records must enable citizens to request correction of inaccurate data without bureaucratic barriers.
Rights handling must be documented, time-bound, and reviewable.
5. Define Retention & Erasure Policies
Align retention periods with statutory mandates (e.g., audit laws, archival requirements) and implement automated deletion workflows.
Legacy pension or welfare databases without deletion triggers create perpetual risk surfaces.
Retention without purpose is liability accumulation.
How DPDP Compliance Protects Public Companies and PSUs
For PSUs and public companies, DPDP compliance reduces litigation risk, audit objections, reputational damage, and international investment scrutiny. Structured data governance improves operational clarity and aligns with global data protection benchmarks like GDPR.
Investors look at governance metrics.
Public companies processing digital services — banking, telecom, utilities — face higher scrutiny.
1. Audit & CAG Scrutiny Readiness
PSUs face oversight from CAG, parliamentary committees, and vigilance bodies. Demonstrating DPDP compliance strengthens audit defensibility and reduces adverse observations in governance reports.
2. Reduced Litigation & Writ Petition Exposure
Citizen data breaches in public companies often result in PILs or writ petitions.
Strong compliance architecture mitigates judicial intervention and reputational escalation.
3. Vendor & Outsourcing Risk Containment
Many PSUs rely on IT integrators. Under DPDP, liability remains with the data fiduciary. Structured vendor agreements and data processing audits reduce downstream exposure.
4. Strengthened Public Trust in Digital Governance
Digital initiatives — from smart cities to digital banking — rely on citizen trust. Transparent data governance improves adoption and reduces resistance to digitization programs.
Compliance is not a burden. It is institutional armour.
The Practical Roadmap for Government Sector DPDP Readiness
Build a fortress. Not a patchwork.
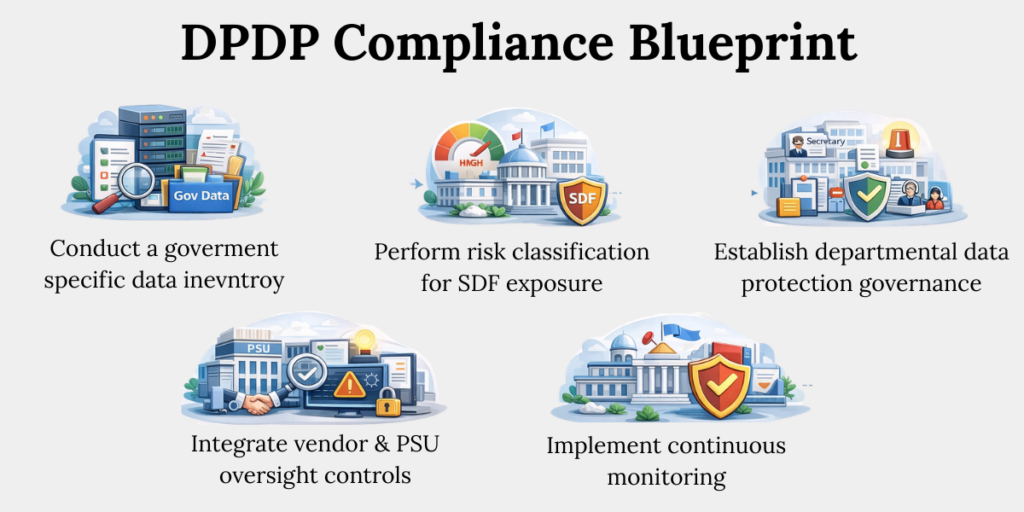
Here is the compliance blueprint:
1. Conduct a Government-Specific Data Inventory
Create a centralized register of all digital processing activities, including welfare disbursement systems, employee databases, grievance portals, and vendor-managed cloud services.
Map lawful purpose, access hierarchies, and statutory retention obligations to avoid undocumented processing.
2. Perform Risk Classification for SDF Exposure
Assess volume thresholds, sensitivity levels, and dependency of national infrastructure on the system.
Ministries operating nationwide portals should conduct quantitative risk scoring and determine potential impact radius of a breach.
3. Establish Departmental Data Protection Governance
Define clear accountability chains — Secretary-level oversight, designated compliance officers, IT heads, and grievance officers.
Governance structures must be documented through official circulars and administrative orders to ensure enforceability.
4. Integrate Vendor & PSU Oversight Controls
Review all outsourcing contracts for data processing clauses, confidentiality obligations, breach reporting timelines, and subcontracting controls.
Public sector entities must maintain supervisory oversight even where cloud hosting or IT support is outsourced.
5. Implement Continuous Monitoring
Deploy centralized logging, vulnerability assessments, penetration testing, and simulated breach drills.
Government agencies should institutionalize quarterly compliance reviews rather than relying on reactive corrective action.
Compliance is sustained vigilance.
Conclusion
The DPDP Act places measurable accountability on every entity that determines the purpose and means of processing digital personal data — including the State.
For government officials, PSU management, and administrative leaders, this is not merely a regulatory development. It is a governance reform mandate.
DPDP compliance strengthens administrative integrity, audit resilience, and citizen trust in digital governance systems. It prepares institutions for scrutiny — from regulators, courts, auditors, and the public.
The path forward is clear: Assess your exposure. Build institutional controls. Operationalize accountability.
Action today prevents enforcement tomorrow.
Key Takeaways
- The DPDP Act applies to the government sector, and ministries, PSUs, and public companies can be treated as data fiduciaries.
- Exemptions are limited and conditional, not automatic protection for all government departments.
- DPDP is a structural risk issue for govt bodies due to large citizen databases and interconnected systems.
- Some government entities may be classified as Significant Data Fiduciaries, triggering stricter obligations like DPOs and audits.
- Core compliance requires security safeguards, breach reporting, rights handling, and proper data retention controls.
- For PSUs and public companies, DPDP compliance reduces audit, litigation, and vendor risks.
- A clear roadmap—data inventory, risk assessment, governance setup, and monitoring—is essential for readiness.
Related Blog
- https://www.privacyglobal.org/blog/data-inventory-dpdp-compliance
- https://www.privacyglobal.org/blog/how-to-become-dpdp-compliant-checklist